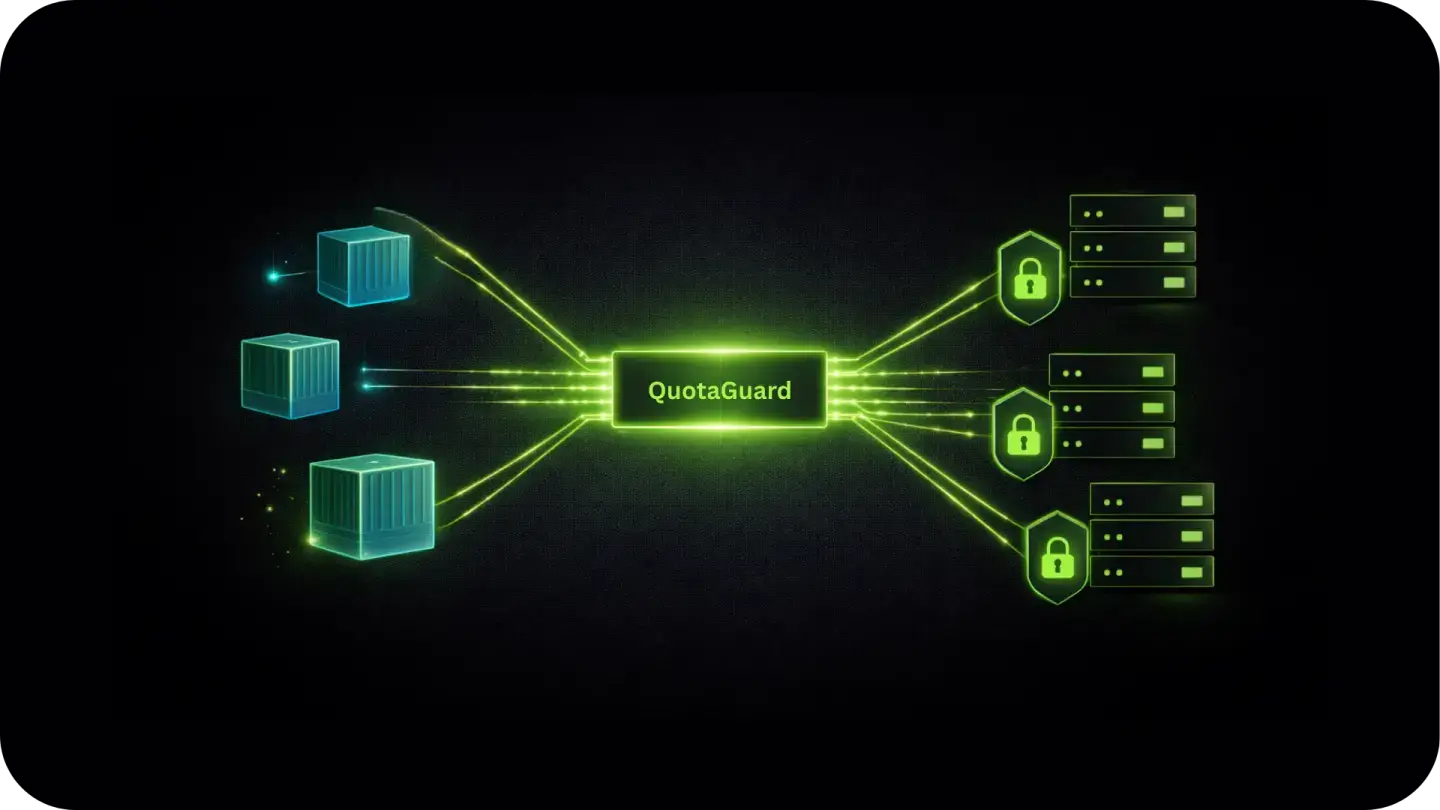
Inbound & Outbound Static IPs for Railway Applications
Bridge Railway services to firewalled databases, internal APIs, and enterprise partners with a dedicated, verifiable network identity.
Eliminate connection rejections from security groups and IP allowlists without moving off Railway or managing your own NAT infrastructure.
Enterprise Connectivity & Allowlisting
Railway services run on shared cloud infrastructure where outbound IP addresses rotate on every redeploy, restart, and scaling event.
Note: QuotaGuard is designed for connecting Railway services to IP-restricted B2B resources like SQL databases, internal APIs, and enterprise gateways. This solution is not intended for scraping consumer sites that block cloud infrastructure.
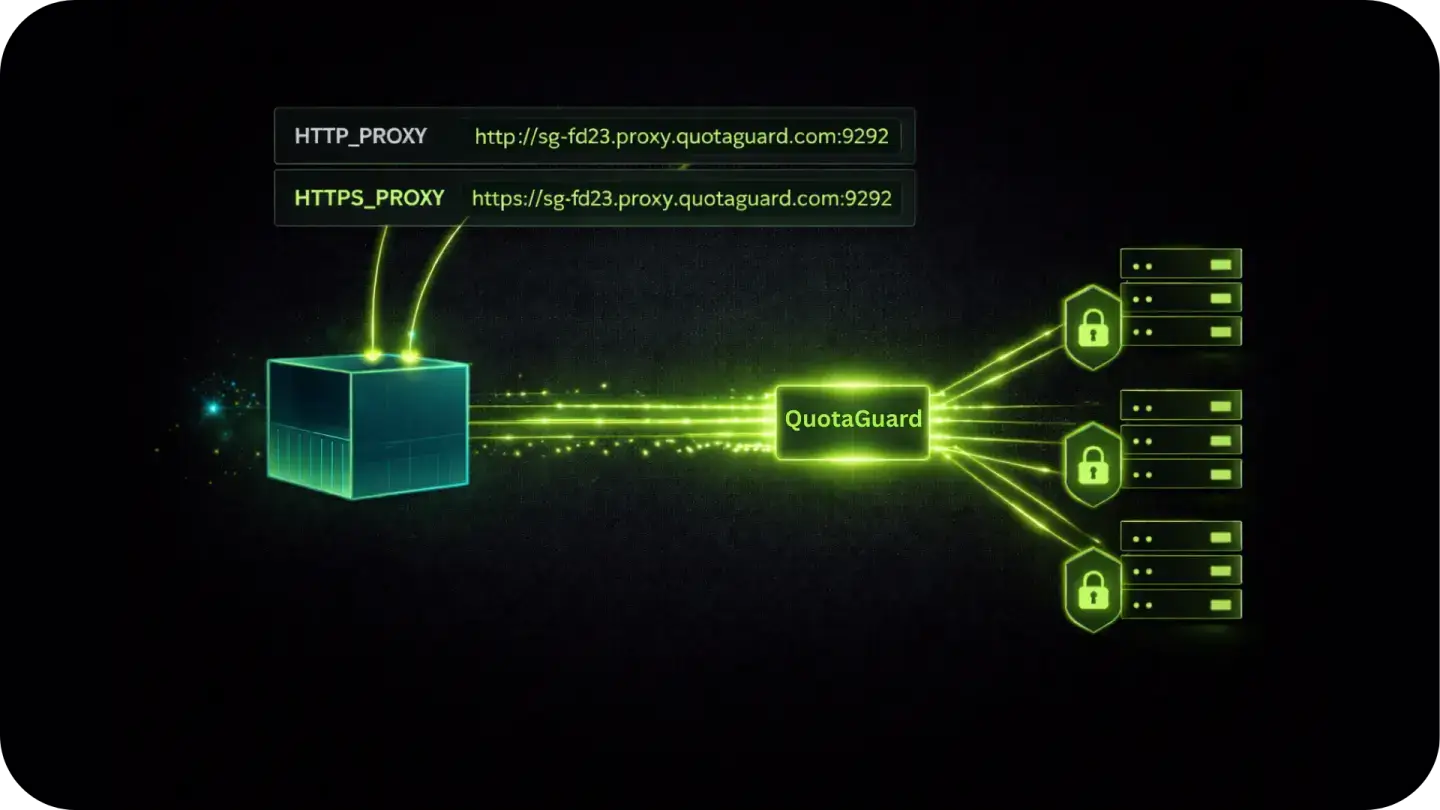
Native Outbound Configuration
QuotaGuard integrates directly with Railway's environment variable system.
No changes to your deployment pipeline, Dockerfile, or service configuration beyond setting two variables.
Environment Variable Injection
Add your QuotaGuard connection string to Railway's variable dashboard as HTTP_PROXY and HTTPS_PROXY.
Most HTTP libraries in Node.js, Python, Ruby, and Go respect these automatically. Redeploy once. Every outbound request routes through your static IP from that point forward.
QGTunnel for Database Connections
For raw TCP connections to PostgreSQL, MySQL, or MongoDB (where an HTTP proxy isn't enough), QGTunnel provides transparent SOCKS5 proxying.
Wrap your Railway start command with QGTunnel and your database driver connects to the original hostname while traffic exits from your static IPs. No application code changes required.
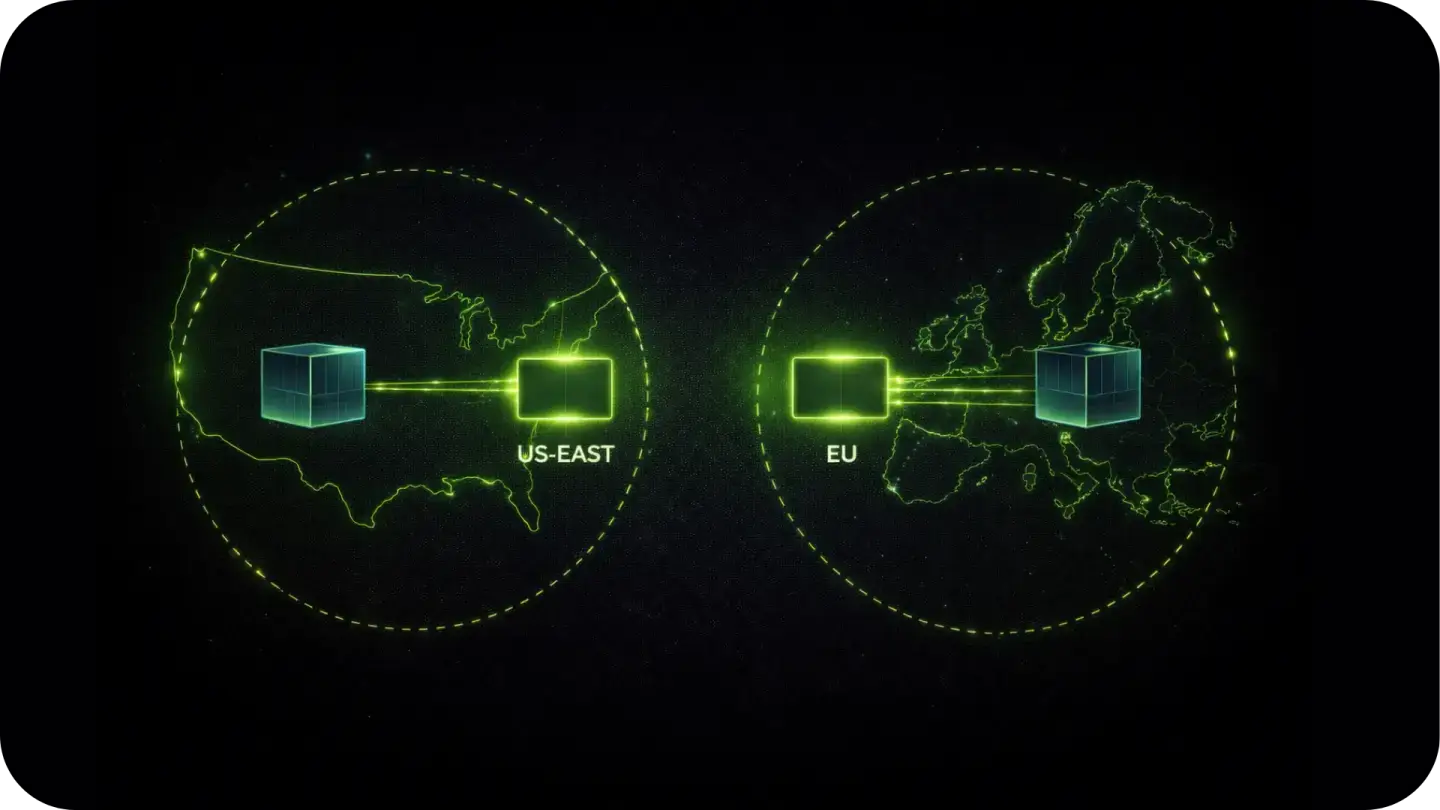
Per-Environment Isolation
Use separate QuotaGuard connection strings for staging and production Railway environments.
Keep development traffic completely separate from live production data, and verify firewall connectivity in staging before it matters in production.
FAQs
Technical Configuration and Setup for Railway Apps
Railway Pro includes a shared static outbound IP you can enable per service. It's free with the plan and works for many use cases.
The difference is that shared IP is used by other Railway Pro customers on the same infrastructure.
QuotaGuard provides two dedicated IPs that belong exclusively to your account.
If your security model requires IP isolation (meaning you need to guarantee that only your service can reach a particular endpoint), dedicated IPs are the right choice.
If IP isolation isn't a requirement, Railway's built-in option is worth trying first.
Make a GET request to https://ip.quotaguard.com from within your Railway service after configuring the proxy.
The response returns the IP your request came from. It should match one of your two static IPs shown in the QuotaGuard dashboard. Run it a few times and you'll see both IPs in rotation.
Yes, via QGTunnel. The HTTP proxy handles HTTP and HTTPS traffic. For raw TCP connections to PostgreSQL, MySQL, or native MongoDB drivers, QGTunnel intercepts those connections transparently and routes them through your static IPs.
Download QGTunnel, configure a tunnel in the QuotaGuard dashboard for your database host and port, then start your Railway service with bin/qgtunnel your-start-command.
See the Railway static IP setup guide for the full configuration.
Yes. The static IPs are assigned to your QuotaGuard account, not to a specific Railway instance or container.
Every time your service starts, it reads the proxy URL from environment variables and connects through the same two IPs.
Your partners never need to update their allowlists after the initial setup.
Routing through a proxy adds one network hop. In the same region, that's typically 10 to 20ms. Cross-region adds 50 to 100ms.
Select a QuotaGuard region that matches your Railway service region to keep latency minimal. For most API calls and database queries, this is imperceptible.
Yes. You can use the same QuotaGuard credentials across multiple Railway services in the same project. All services will share the same two static IPs.
If you need different IPs for different services (for example to isolate production from staging at the network level), use separate QuotaGuard subscriptions.
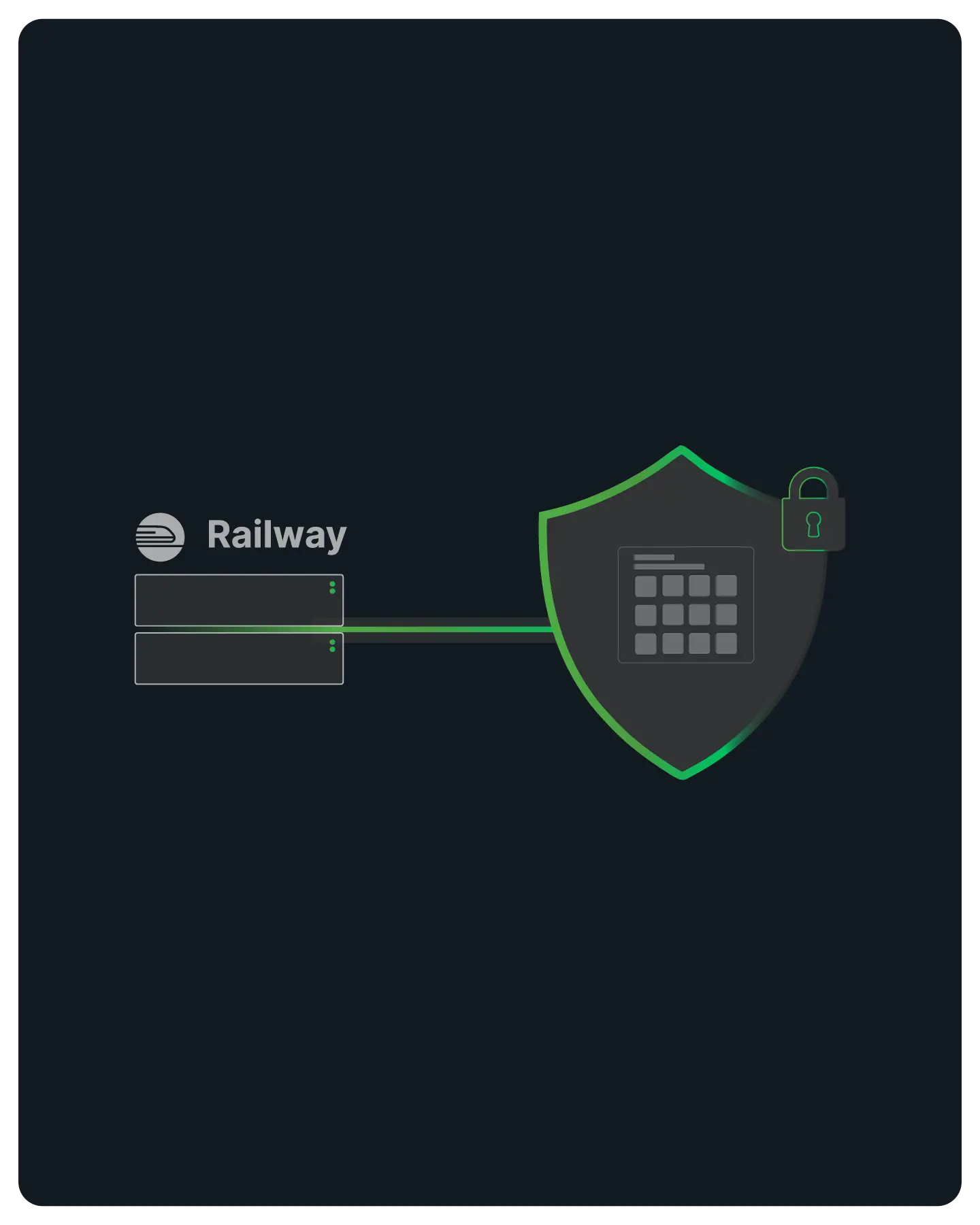
Yes. Railway environment variables are encrypted and only injected at runtime.
Store your proxy URL as a Railway variable rather than hardcoding it in your Dockerfile or application code.
That way you can rotate credentials without a code change or rebuild.
Still have questions?
We don’t outsource Support to non-Engineers.
Reach out directly to the Engineers who built Shield to discuss your specific architecture, integration challenges, or compliance constraints here 👇
🚀 Ready to Get Started? Choose Your QuotaGuard Path
QuotaGuard STATIC
QuotaGuard SHIELD
Trusted by Engineering Teams Everywhere
Reliability Engineered for the Modern Cloud
For over a decade, QuotaGuard has provided reliable, high-performance static IP and proxy solutions for cloud environments like Heroku, Kubernetes, and AWS.
Get the fixed identity and security your application needs today.