Setting up HTTPS with QuotaGuard Static IP's
We suggest you go with the SOCKS proxy using our QGTunnel software.
Here are the setup instructions to get you started.
Step 1. Download QGTunnel and Save to Root of Your Project
Download and extract the qgtunnel package in the root directory of your app:
$ curl https://s3.amazonaws.com/quotaguard/qgtunnel-latest.tar.gz | tar xz
Step 2. Log in to QuotaGuard Dashboard and Create the Tunnel
Login to our Admin Dashboard and go the Tunnels page to setup the tunnel.
Click Create a Tunnel. You should reach this screen below.
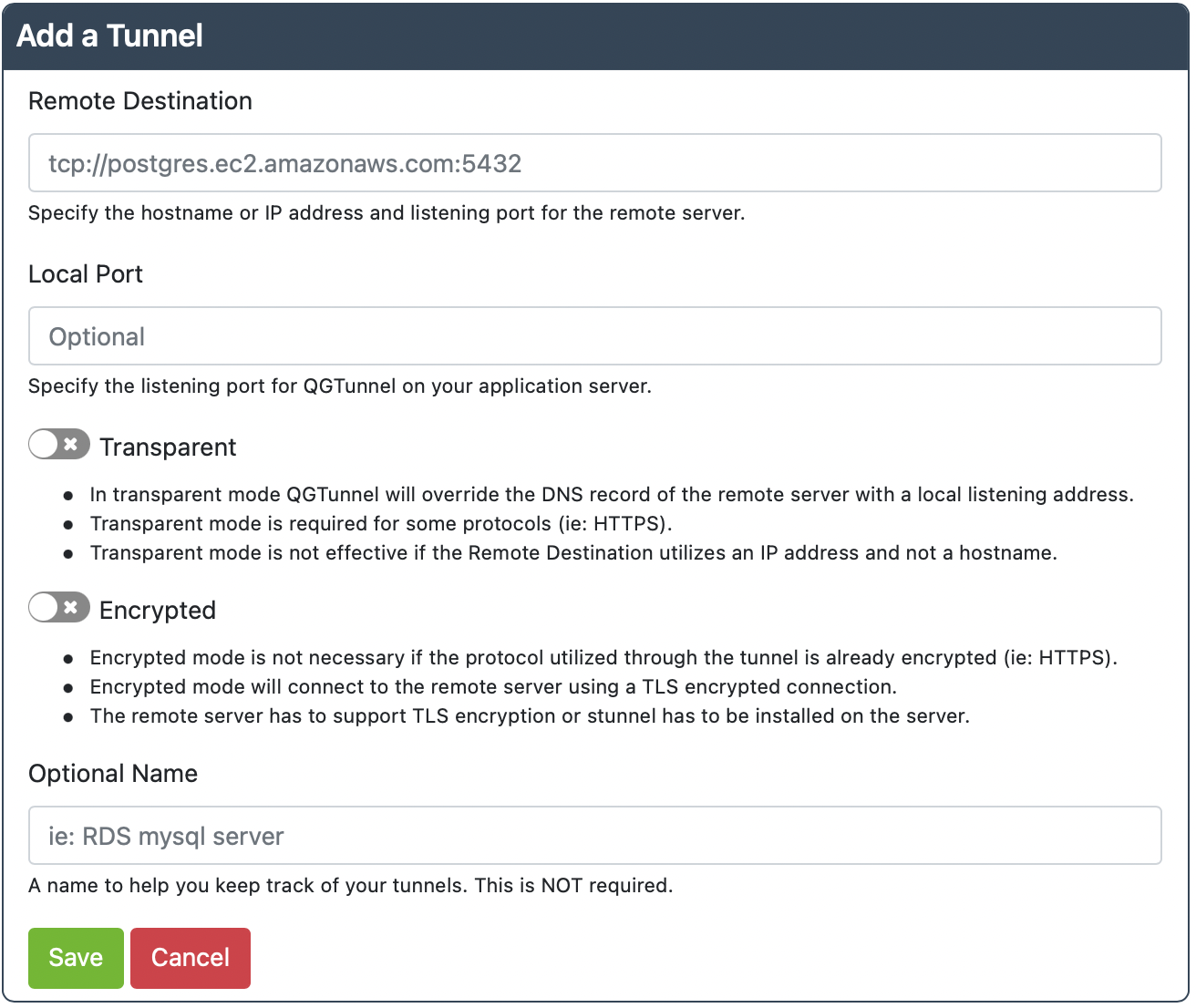
Remote Destination: tcp://hostname.for.your.server.com:443
Local Port: 4433
Transparent: true
Encrypted: false
This setup assumes that your server is located at “hostname.for.your.server.com” and is listening on port 3306 (the default MySQL port).
The Local Port is the port number that QGTunnel will listen on. In this example we set it to 4443, because port 443 is probably in use on the localhost and it is also in the reserved port range (0-1023).
Transparent Mode allows QuotaGuard to override the DNS for hostname.for.your.server.com to 127.0.0.1, which redirects traffic to the QGTunnel software. This means you can connect to either hostname.for.your.server.com or 127.0.0.1 to connect through the QGTunnel.
You will likely require transparent mode for HTTPS connections, as most certificates are signed by hostname and will require the HTTP request to be bound for that hostname.
Encrypted mode is disabled because HTTPS is already encrypted and you will not want to waste your time setting up additional end-to-end encryption.
Creating the tunnels in the dashboard is for convenience. Please see the last step (Harden Your Setup) for how to remove this dependency from your system.
Step 3. Change Your Code to Connect Through the Tunnel
Given the example above, you will now need to connect using the new port number in your URL.
For example, if you previously were trying to connect to:
https ://hostname.for.your.server.com/some/long/path?var=1&var2=3
Now you will want to connect to:
https://hostname.for.your.server.com:4443/some/long/path?var=1&var2=3
Step 4. Setup the Environment Variable QUOTAGUARDSTATIC_URL to be equal to your Connection URL in the Setup page of our dashboard.
If you added us from a cloud provider (Azure, Cloudfoundry, Heroku, AWS, IBM Cloud, Pivotal, etc) then this is usually done for you.
Please note that QGTunnel handles converting the HTTP URL and port to the SOCKS5 URL and port. So either of the connection URLs is fine.
Step 5. Commit and Push your Code
Commit and deploy your changes. Be sure to add bin/qgtunnel.
If you are using transparent mode, be sure vendor/nss_wrapper/libnss_wrapper.so is also committed.
Step 6. Troubleshoot Any Problems
By default all fatal errors encountered by the qgtunnel will be logged to your logs.
If this information is not enough you can enable verbose output mode by setting QGTUNNEL_DEBUG environment variable to true and restart the application while watching the logs.
Send any information in the logs (please redact any credentials, including your QuotaGuard connection URL) to our Support so we can help figure out the problem with you.
Step 7. VERY IMPORTANT - Download QGTunnel Configuration
This step is highly recommended as we do not have any SLA on our website, which can be out due to maintenance at any time.
By default qgtunnel will try to fetch configuration from the QuotaGuard API, but it also supports local configuration.
You can download a configuration file from the Dashboard by pressing Download Configuration on the Tunnels page.
Place the downloaded file into the root directory of your project under the .qgtunnel filename, commit and deploy.
With this file your application will not depend on the availability of our website during application startup.
Getting Help
The SOCKS wrapper is not straight forward to set up, or debug, so if you have any issues just get in contact with our Support and we’ll help you out.