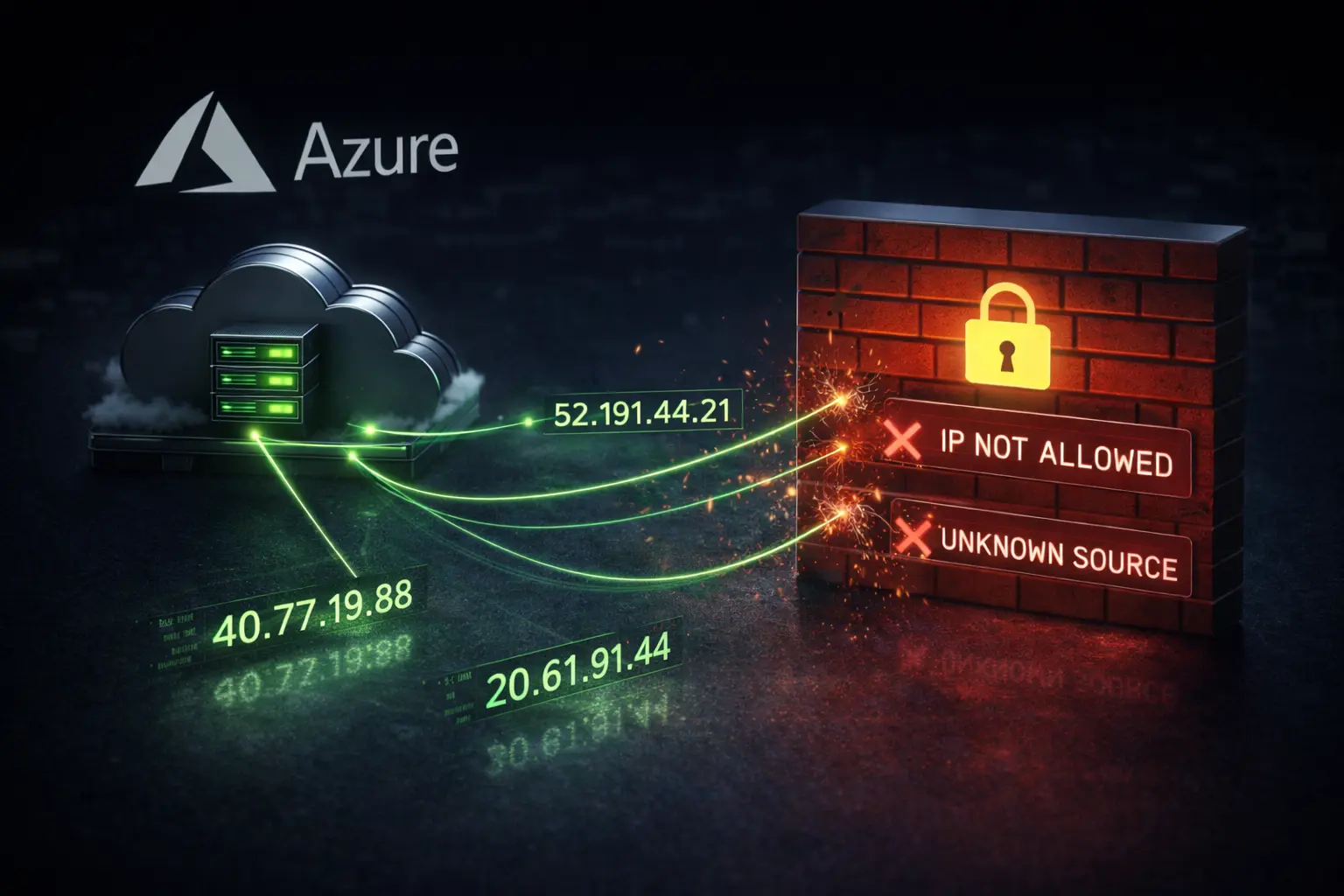
Zapier doesn't have a static IP. It runs on AWS us-east-1, spinning up instances on demand across a massive pool of addresses. When your API partner or firewall requires a whitelisted IP, that's a problem.
The official guidance in the Zapier community forum is to whitelist the entire AWS us-east-1 IP range. That's millions of addresses. Those addresses aren't exclusive to Zapier. Anyone can rent an AWS instance in us-east-1 and hit your firewall from the same range you just opened.
Why Zapier Can't Give You a Static IP
This isn't a bug or a missing feature. It's how cloud infrastructure works. Zapier provisions compute resources dynamically. The IP your Zap uses today might belong to someone else's workload tomorrow.
The Zapier community has been asking about this for years. People build Zaps that push data to SFTP servers, connect to SQL Server, wire up WordPress webhooks. The other side always wants a static IP. Zapier can't provide one.
Some people try the User-Agent workaround. Zapier sends a User-Agent: Zapier header with every request. User agents are trivial to spoof. That's not a real security mechanism.
The Fix: A Static IP Proxy
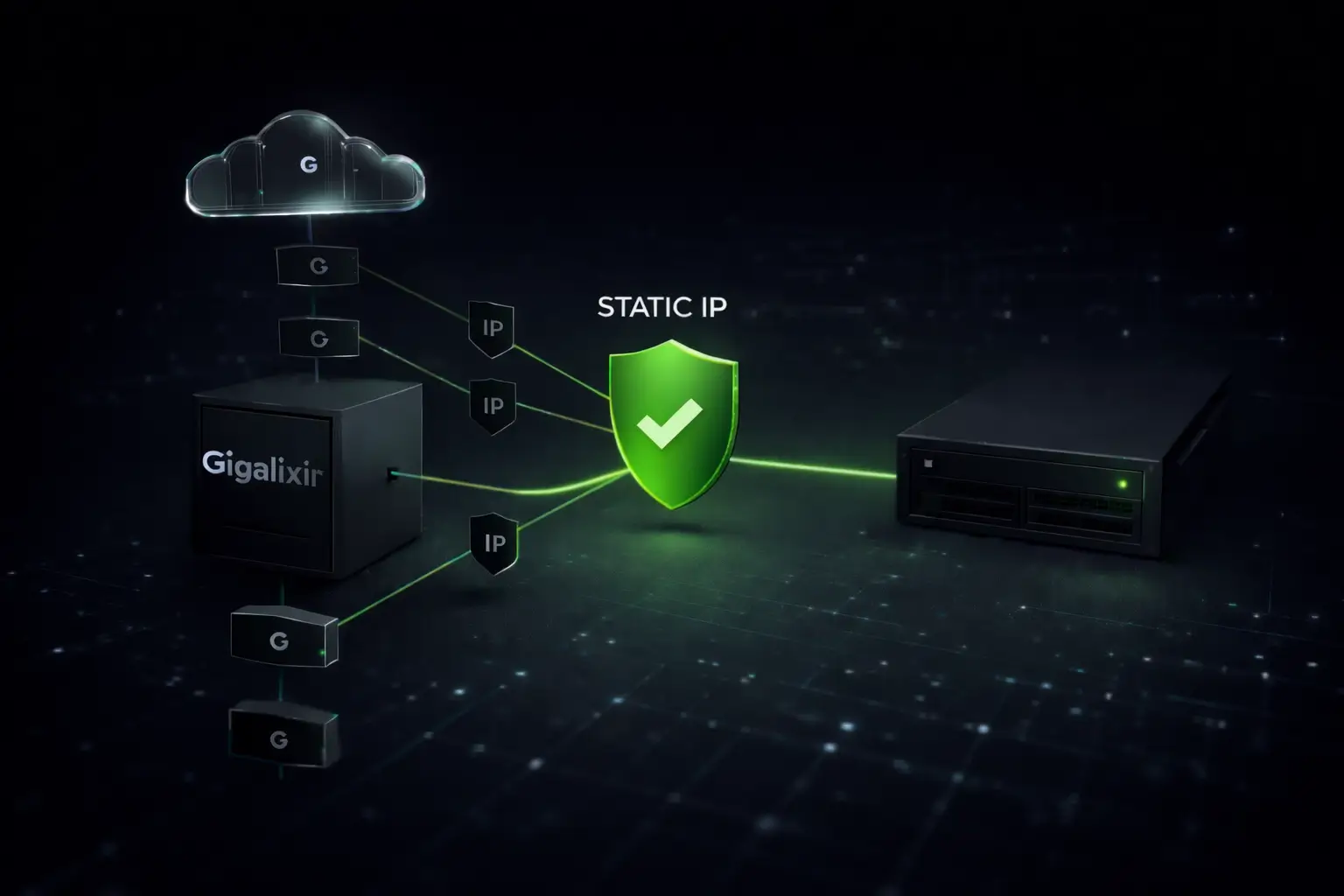
The solution is a proxy between Zapier and your destination. Your Zap sends traffic through it. The proxy has a static IP. You give that IP to your API partner, your SFTP vendor, your database admin.
QuotaGuard Static gives you two load-balanced static IP addresses. You configure your Zap's HTTP request to route through the proxy URL. Every outbound request from that Zap now comes from one of those two IPs. No more whitelisting entire AWS regions.
Common Questions
"Does Zapier use a single IP address I can whitelist?" No. Zapier uses the AWS us-east-1 pool. You need a proxy to get a static IP.
"How do I whitelist Zapier in my WordFence firewall?" Route your Zap through QuotaGuard, then whitelist the two static IPs in WordFence. No CIDR notation gymnastics required.
"Isn't it a security risk to whitelist the entire us-east-1 range?" Yes. It opens your firewall to any AWS customer in that region. A static IP proxy reduces your attack surface from millions of addresses to two.
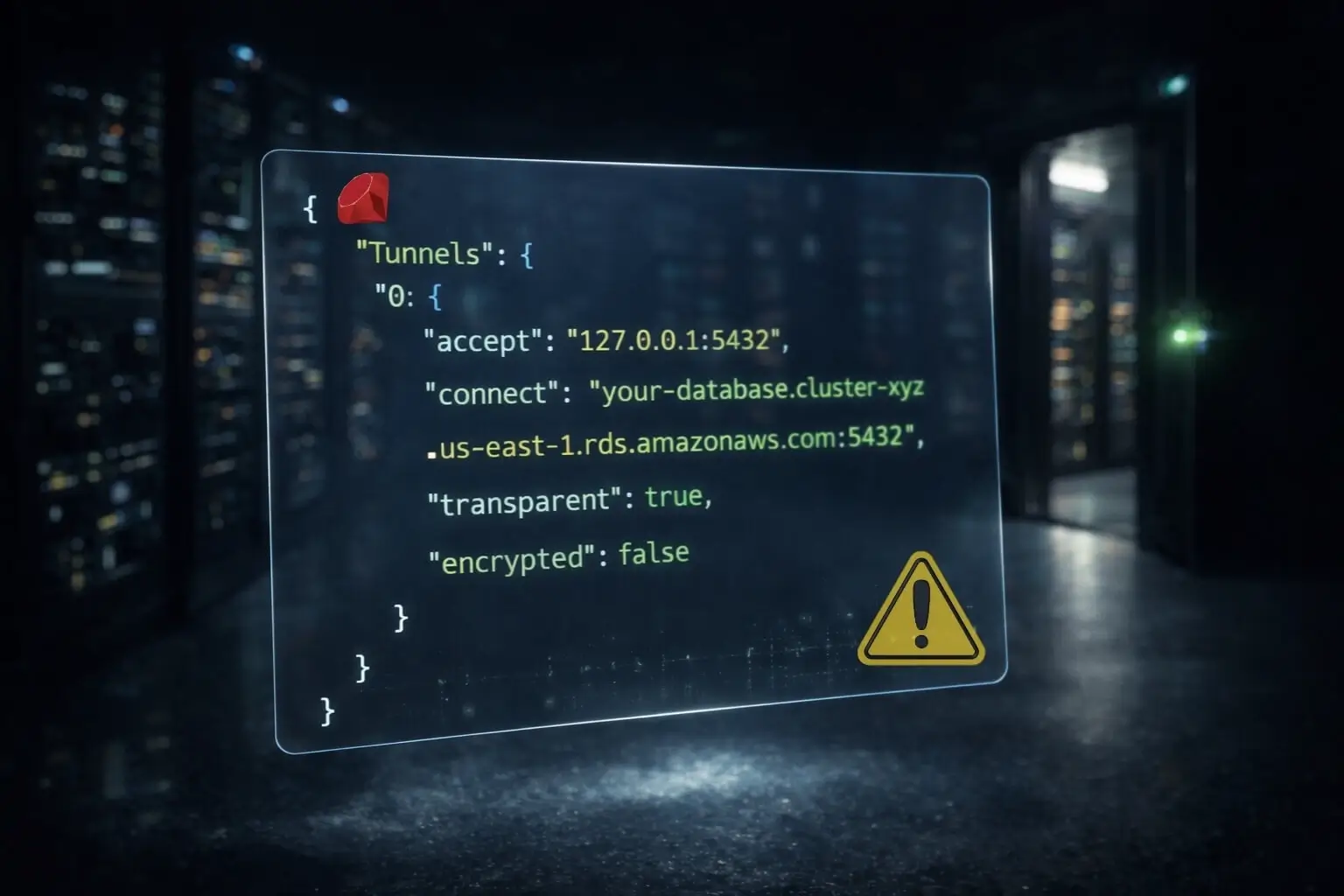
"My Zap connects to SQL Server but port forwarding restrictions block it." SQL Server connections need more than HTTP proxying. QuotaGuard's SOCKS5 proxy and QGTunnel handle TCP-level protocols like database connections. You configure the tunnel to map your local port to the remote SQL Server, and traffic routes through your static IP.
"Can I get a static IP for my Zapier webhook sender?" Yes. QuotaGuard proxies outbound traffic from Zapier through a static IP. Your webhook recipient sees a consistent, whitelistable address.
Setting It Up
This takes about five minutes.
- Sign up for QuotaGuard Static. You get a proxy URL and two static IP addresses immediately.
- In your Zap, use a Webhooks by Zapier action (or Code by Zapier) to route your HTTP request through the proxy URL.
- Give the two static IPs to whoever controls the firewall on the other end.
- For non-HTTP protocols (databases, SFTP), use QuotaGuard's SOCKS5 proxy or QGTunnel for TCP-level connections.
If You're Handling Sensitive Data
If the traffic you're routing through Zapier involves healthcare data (HIPAA), payment card data (PCI-DSS), or personal data subject to GDPR, you need more than a static IP. You need end-to-end encryption.
QuotaGuard Shield uses SSL passthrough. Your data is never decrypted at the proxy layer. Shield also supports BAA signing for HIPAA, and US-only or EU-only data residency so traffic never leaves the jurisdiction your compliance team requires. Shield starts at $29/month.
QuotaGuard Static IP Blog
Practical notes on routing cloud and AI traffic through Static IPs.

.webp)

.webp)










.webp)











.webp)




