SOC 2 Trust Services Criteria CC6.1 covers logical access controls, including network security. During an audit, your assessor will ask how you control outbound network traffic. If you're running on Heroku, Render, Vercel, or another PaaS, this question can be surprisingly hard to answer.
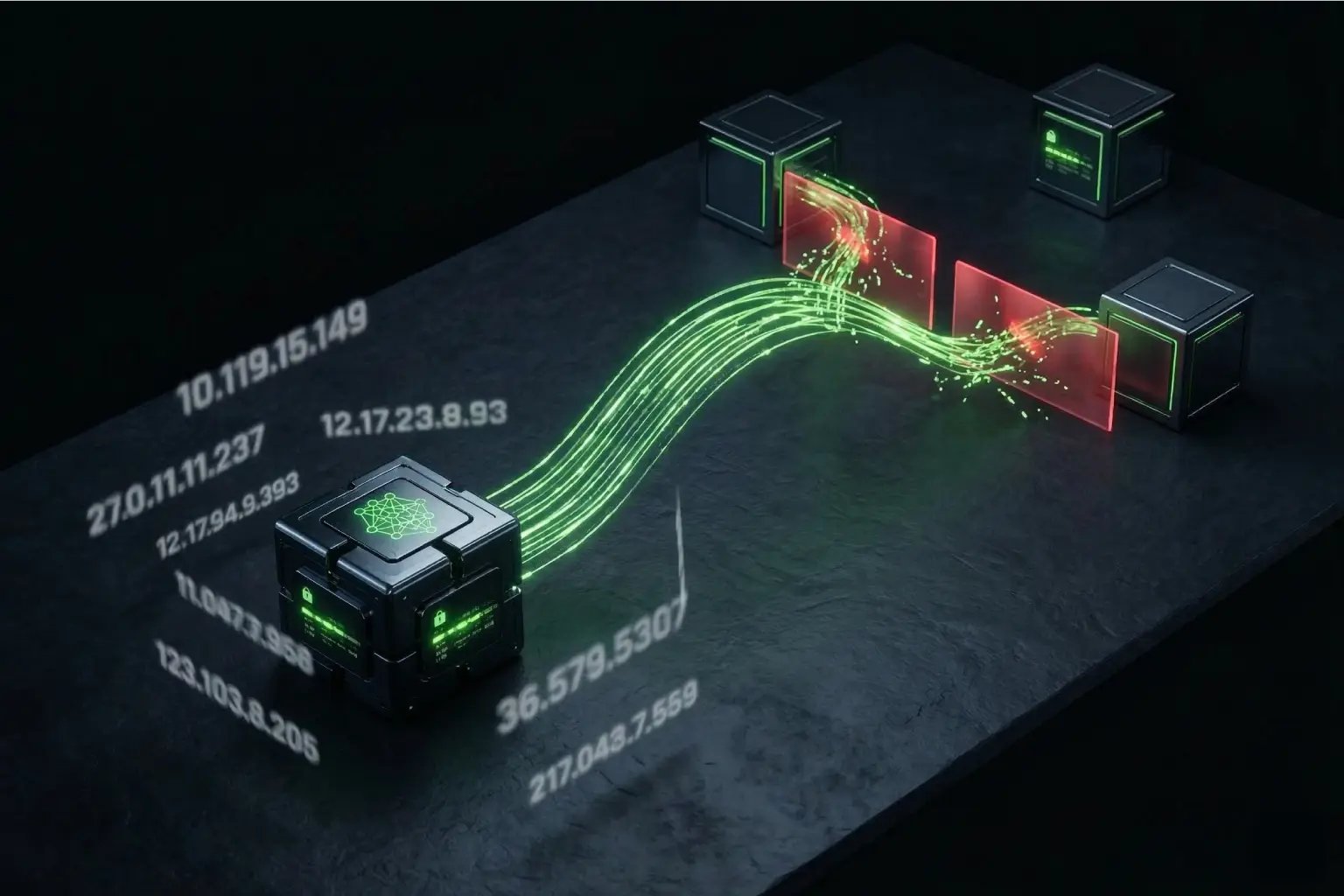
The PaaS Egress Problem
On a traditional server, you know your outbound IP. You document it. You whitelist it with partners. Straightforward.
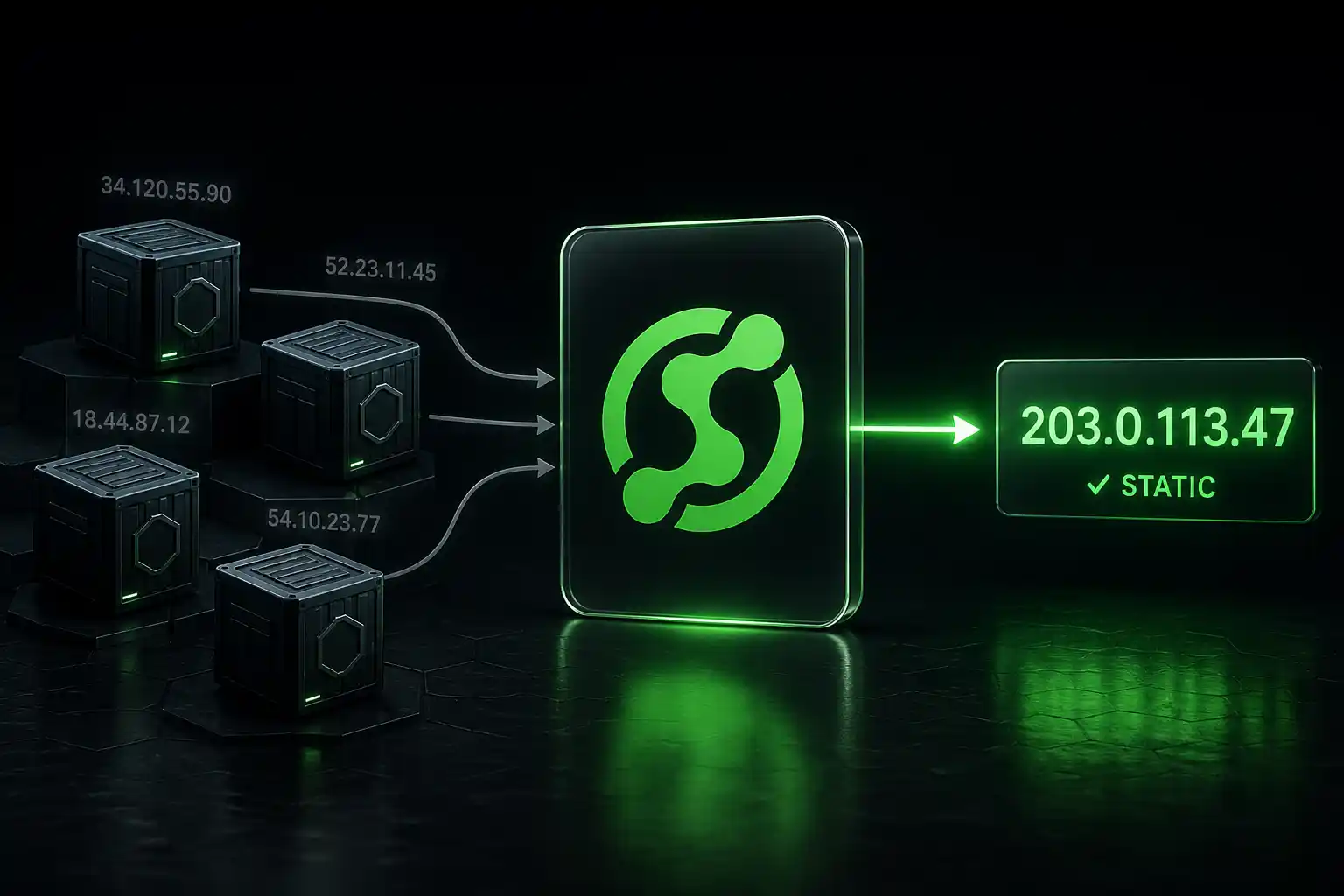
On a PaaS, your outbound IP rotates. It changes with deployments, restarts, and scaling events. You can't tell your auditor which IPs your app uses because they're different every few hours. You can't whitelist them with customer firewalls. And logging exactly what left your infrastructure gets complicated.
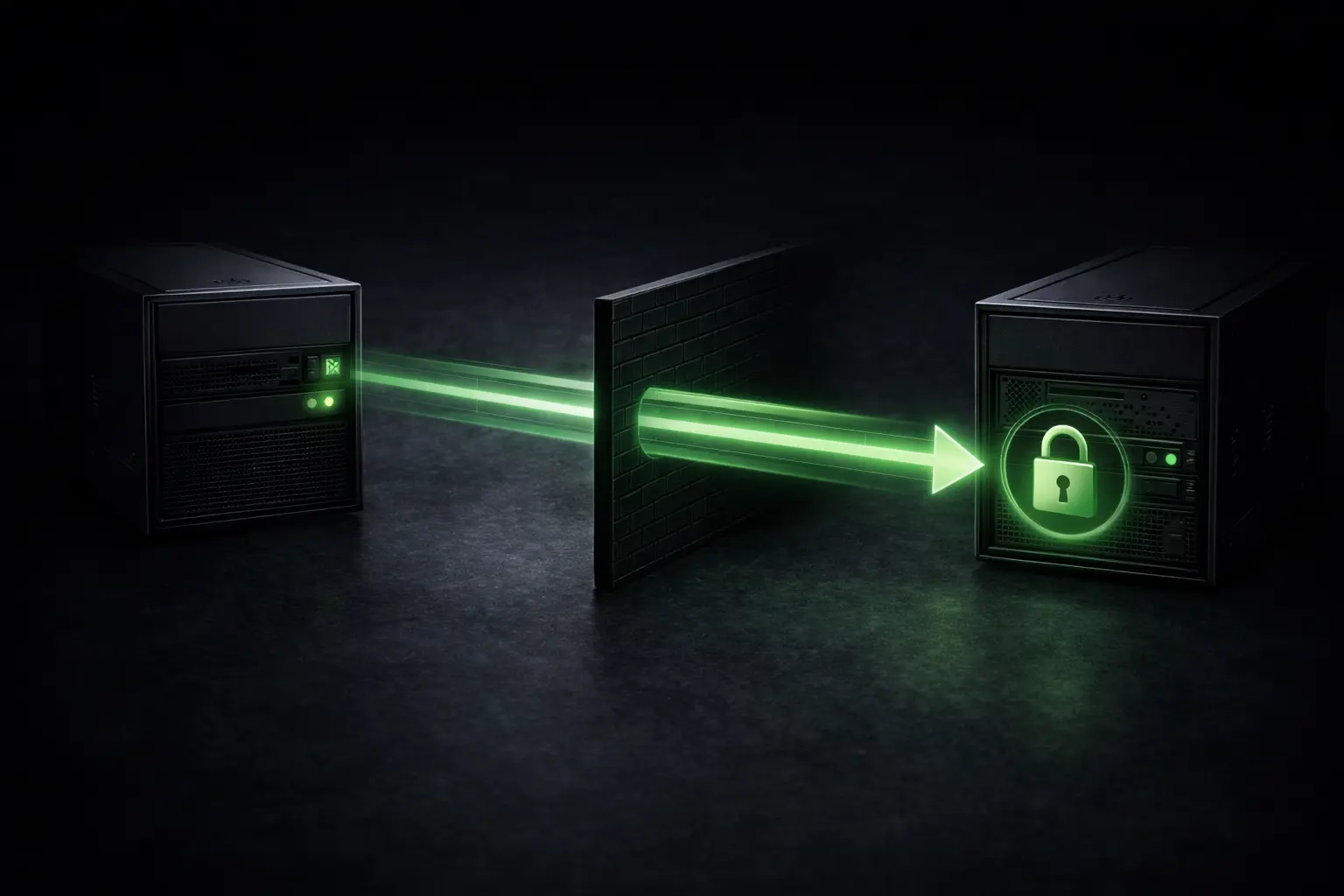
Auditors care about this because CC6.1 requires that sensitive data leaving your infrastructure is controlled, documented, and auditable. Rotating IPs don't meet that standard. The auditor documents it as a finding. Enterprise customers see it on the SOC 2 report.
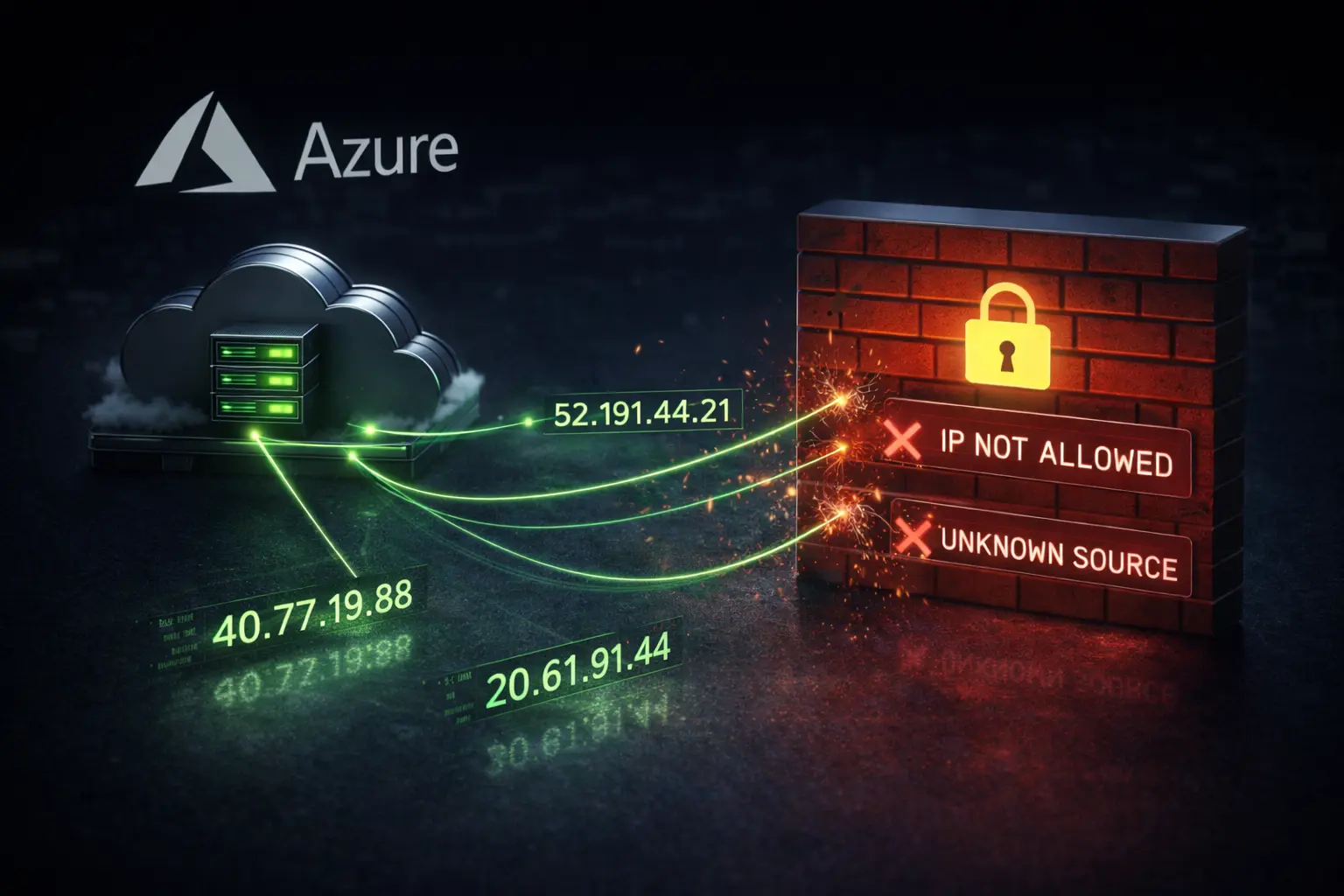
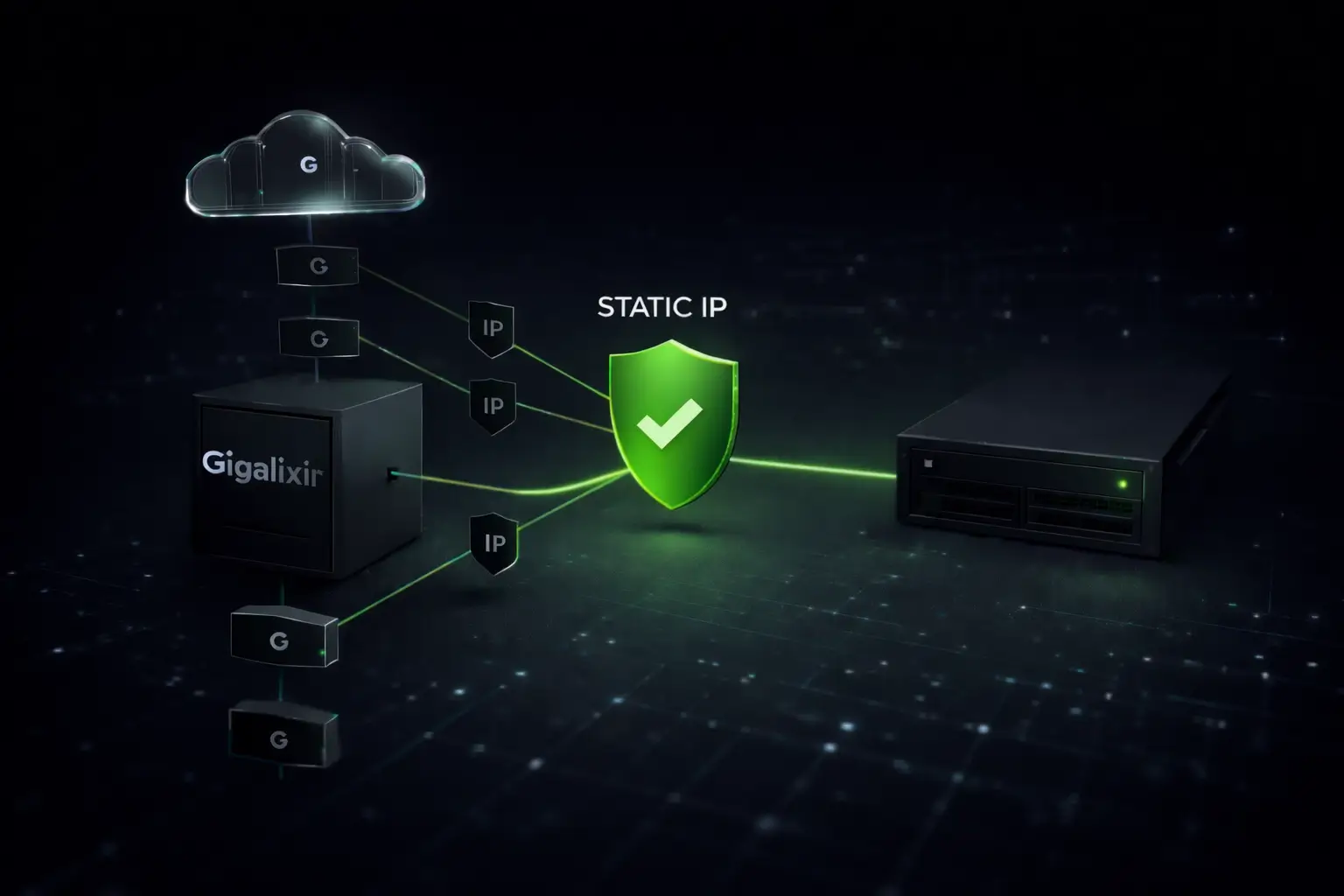
How Static IPs Solve It
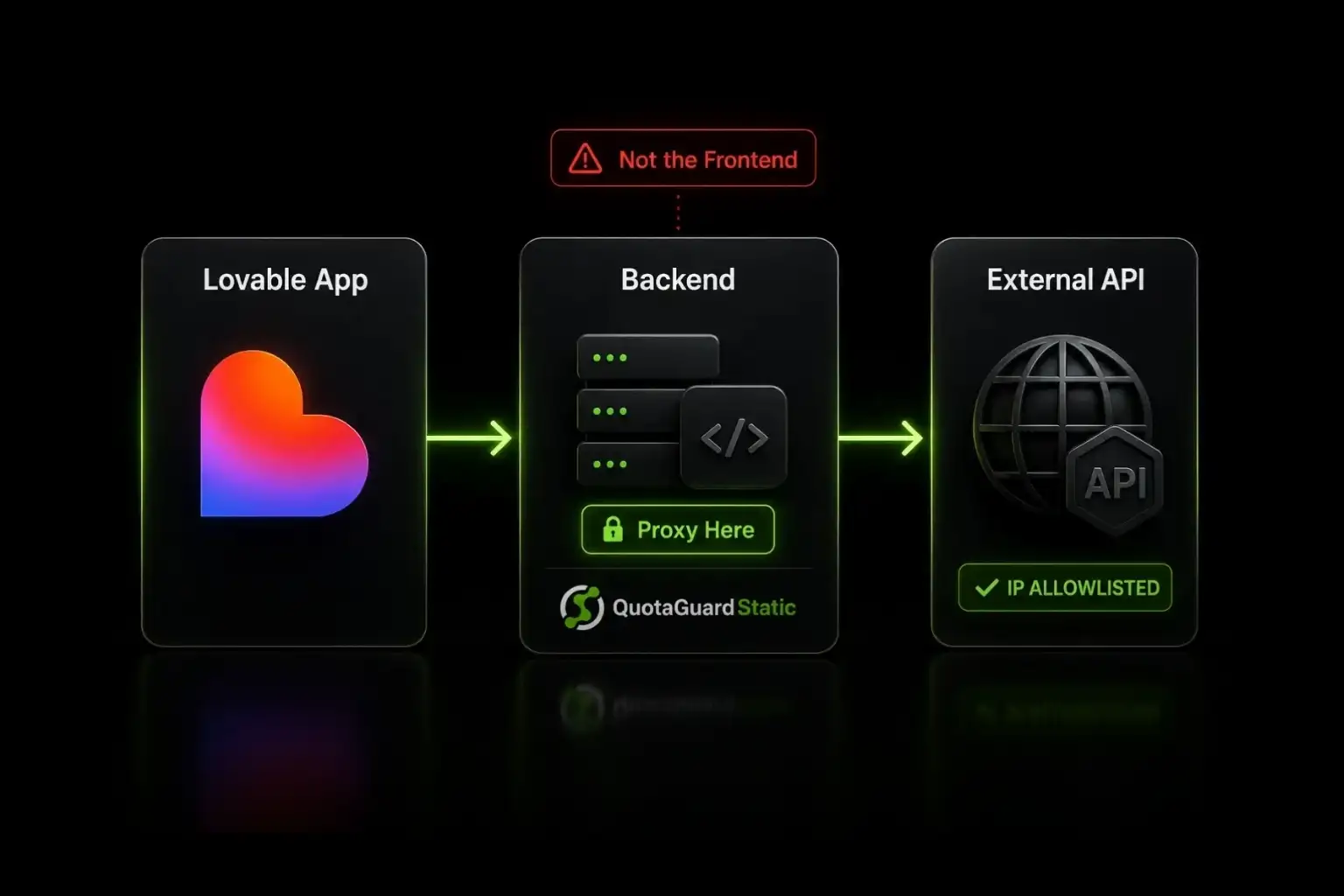
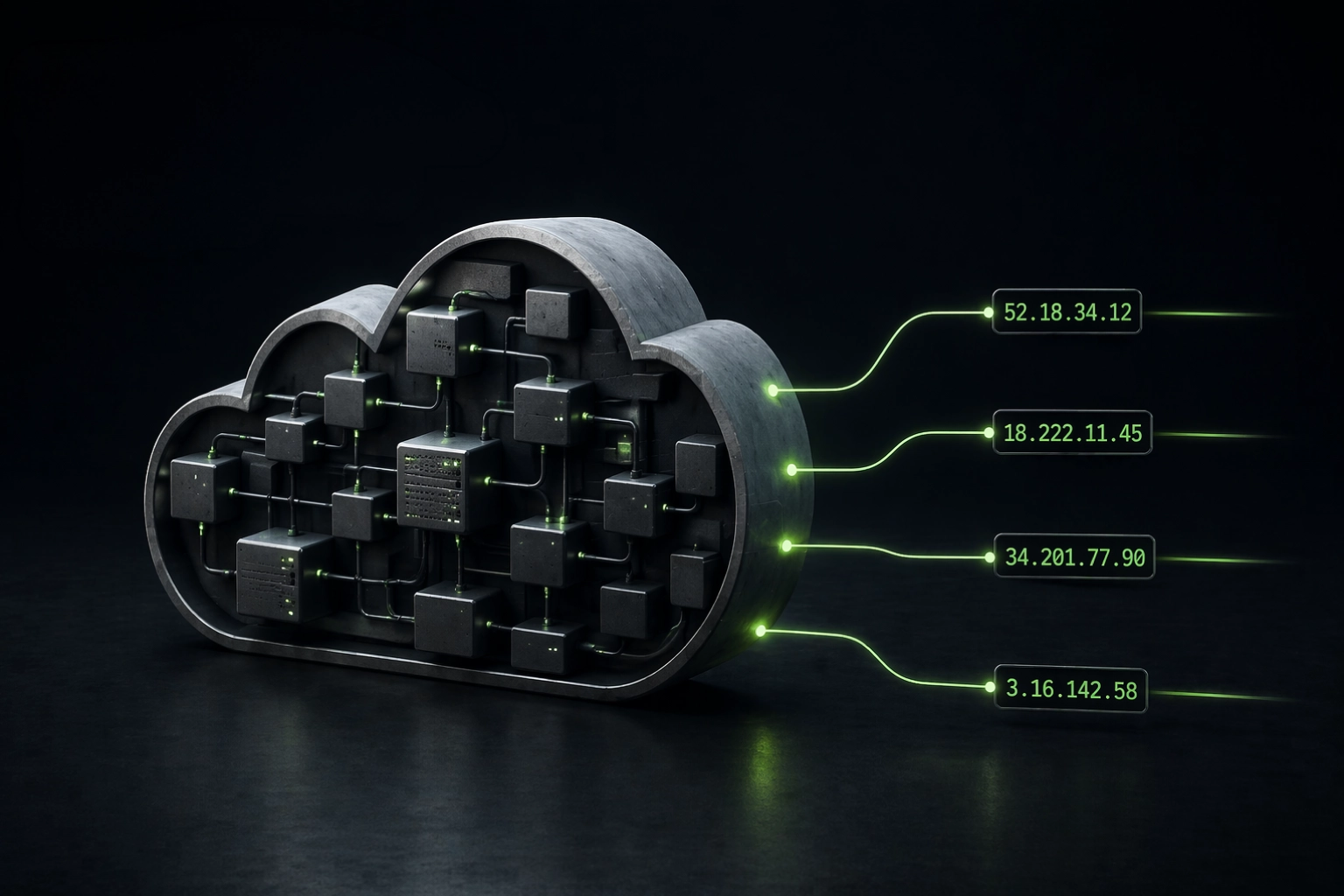
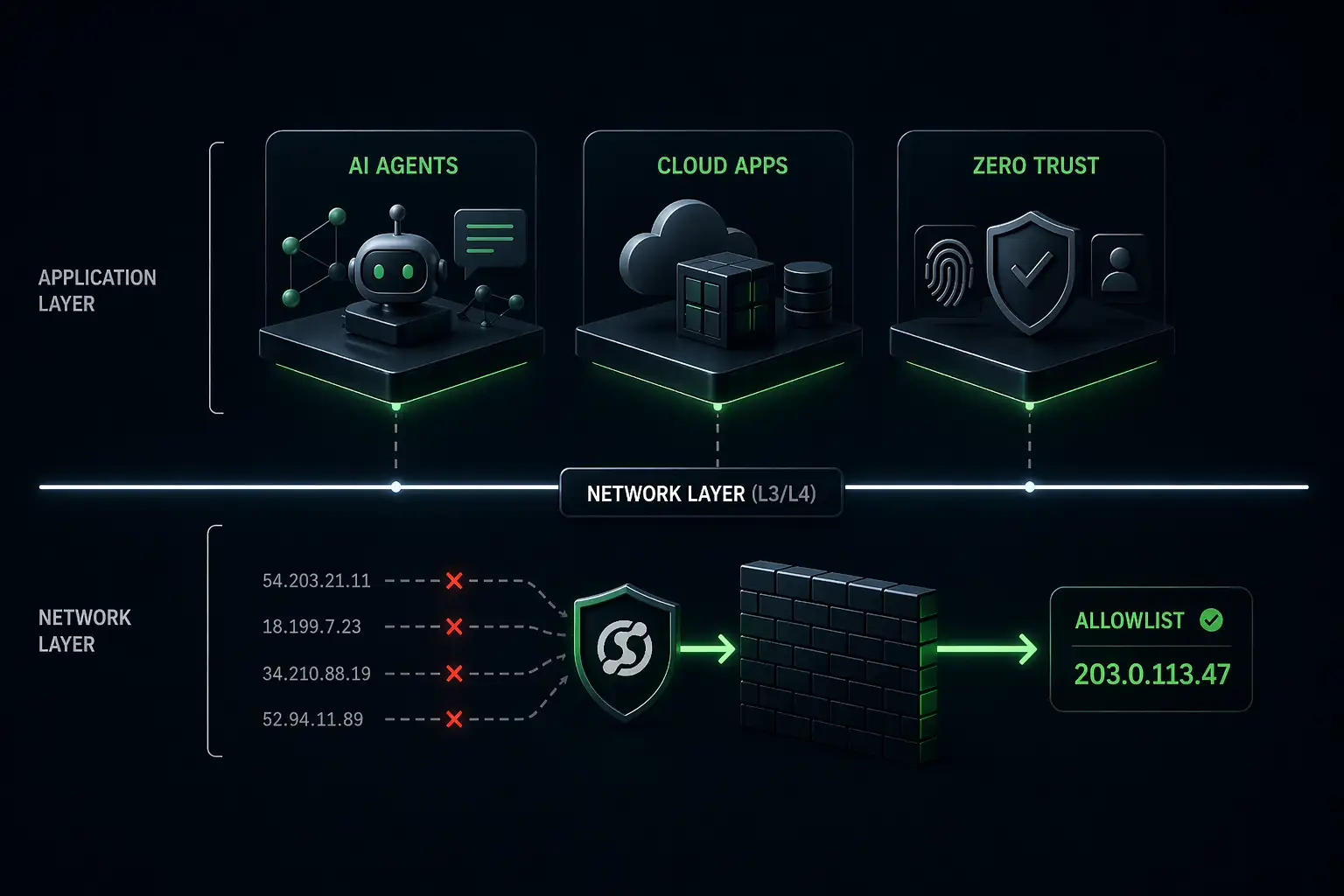
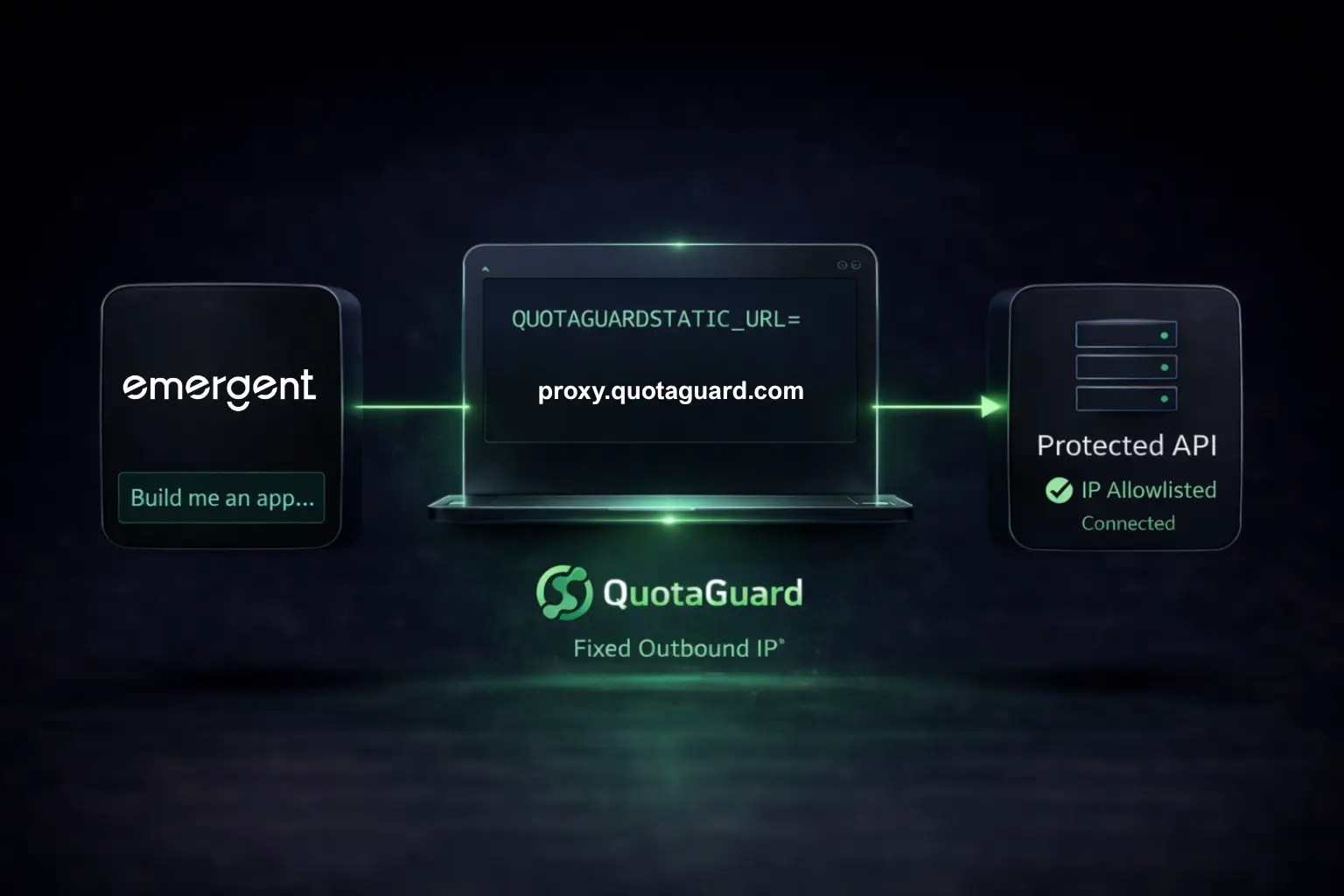
With QuotaGuard Static, your app's sensitive outbound traffic routes through two load-balanced static IPs. Always the same addresses. Always documented. Always auditable.
The setup takes about 20 minutes. Your app makes outbound requests through an HTTP proxy, SOCKS5 connection, or QGTunnel. All traffic routes through our infrastructure. Your auditor gets two IP addresses to document. Your customers get those two IPs to whitelist.
When the auditor asks "How do you control egress?" the answer is: "All sensitive outbound traffic routes through a static proxy with two documented IP addresses. Traffic is logged. Failover is automatic."
That's a clean answer. That's the answer that closes the finding.
What Auditors Want to See
A typical SOC 2 auditor checklist for network controls covers a few key areas.
Traffic documentation. Two static IPs. Listed on your QuotaGuard dashboard. Easy to reference.
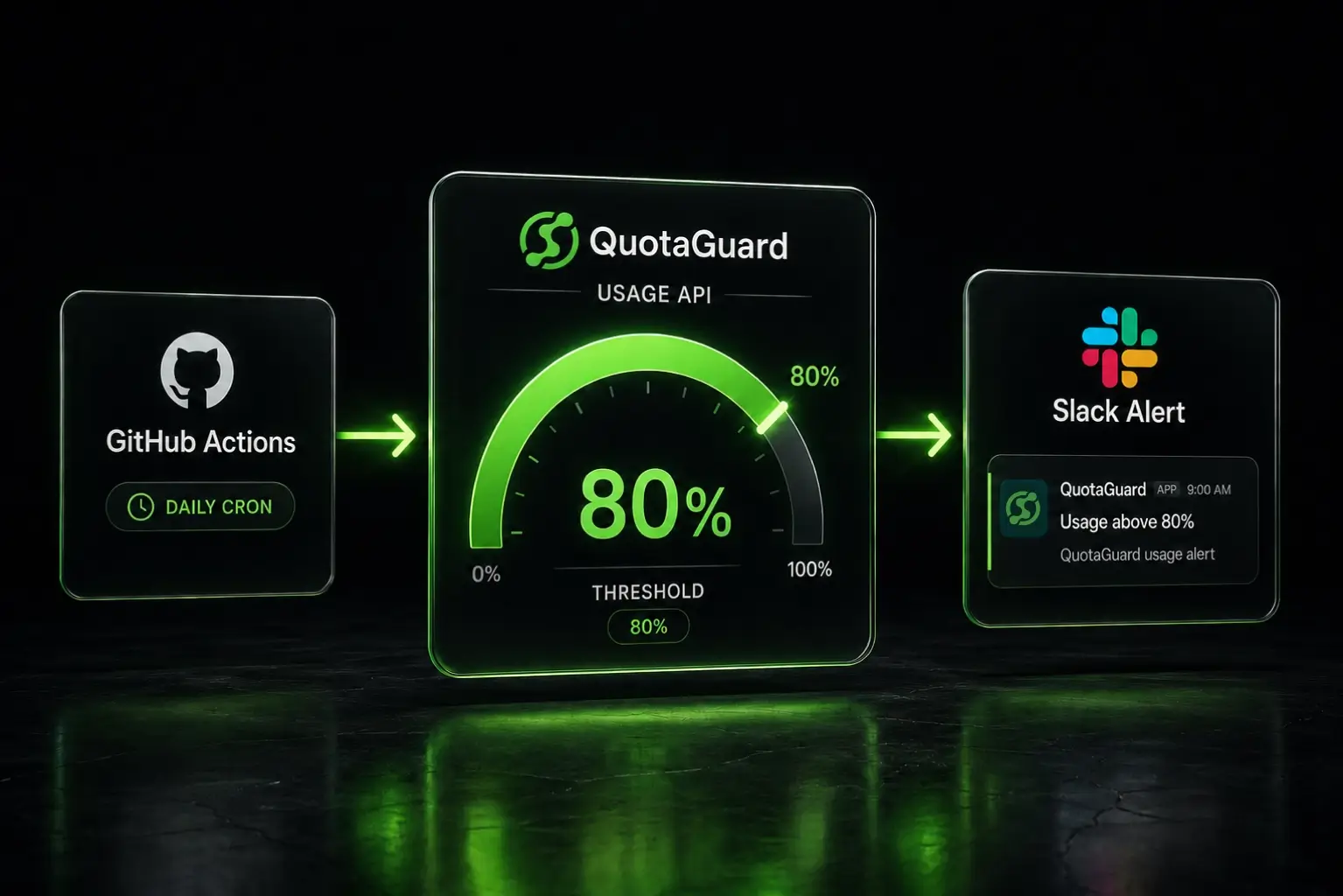
Egress logging. The dashboard shows where traffic is going, where it came from, and when. This is the evidence that outbound traffic is actually controlled.
Change management. Changes to proxy configuration (adding or removing traffic destinations) create a documented audit trail.
Encryption in transit. All traffic through QuotaGuard is encrypted. If your auditor asks for encryption evidence, you have it.
Failover redundancy. Two load-balanced IPs mean if one goes down, the other handles traffic automatically. Built-in resilience.
A Practical Example
A SaaS startup integrates with Slack, Stripe, PagerDuty, and a private customer database. They're on Heroku. Their first SOC 2 Type II audit kicks off.
Without static IPs, the audit conversation is awkward. The team pulls AWS VPC logs, runs netstat commands, and explains that IPs rotate. The auditor notes: "Unable to verify documented egress control points."
With QuotaGuard Static, the conversation takes 10 minutes. All outbound traffic goes through two IPs. The dashboard shows traffic logs. Every request to Slack, Stripe, and PagerDuty is logged. The auditor notes: "Egress control verified."
Platform Support
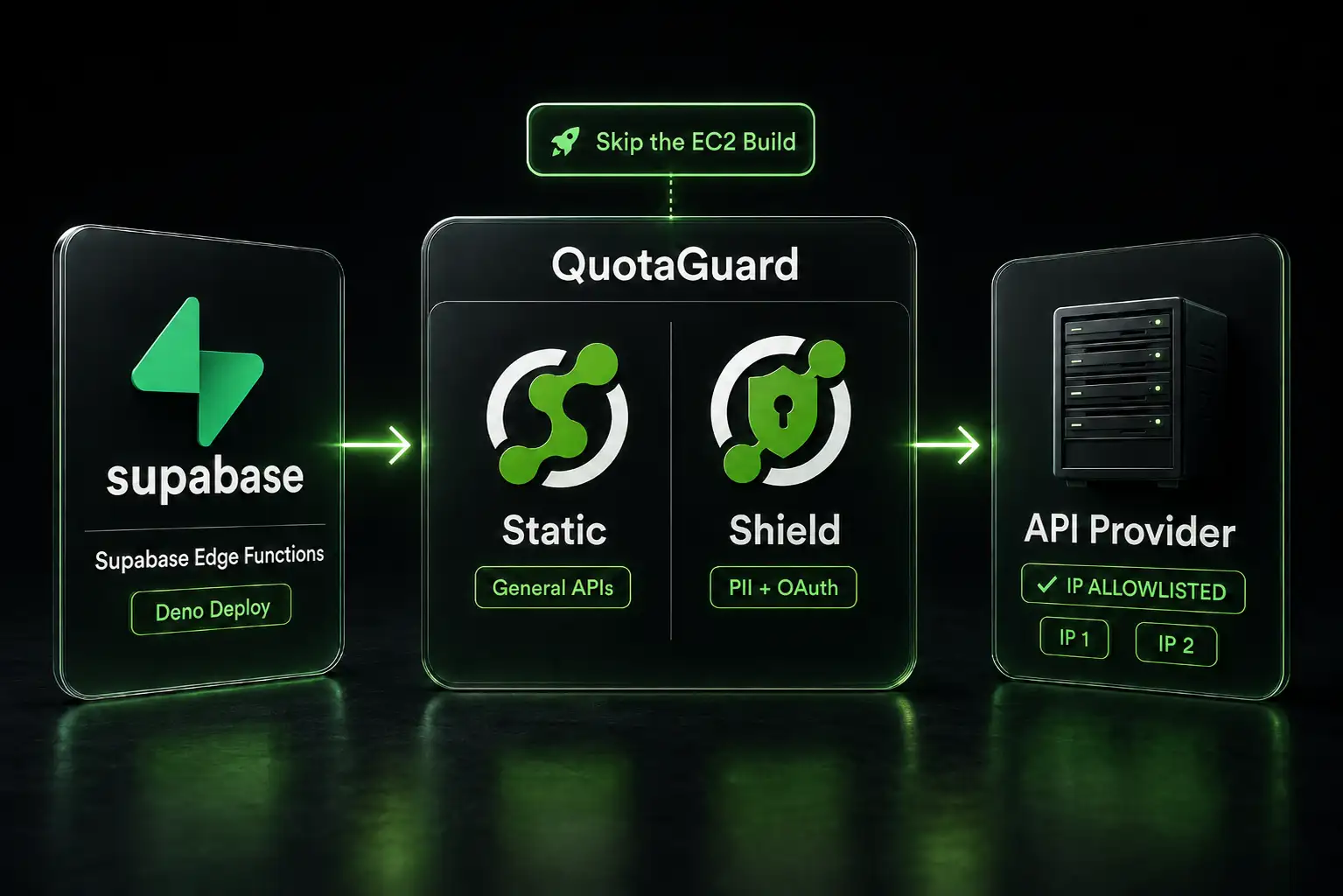
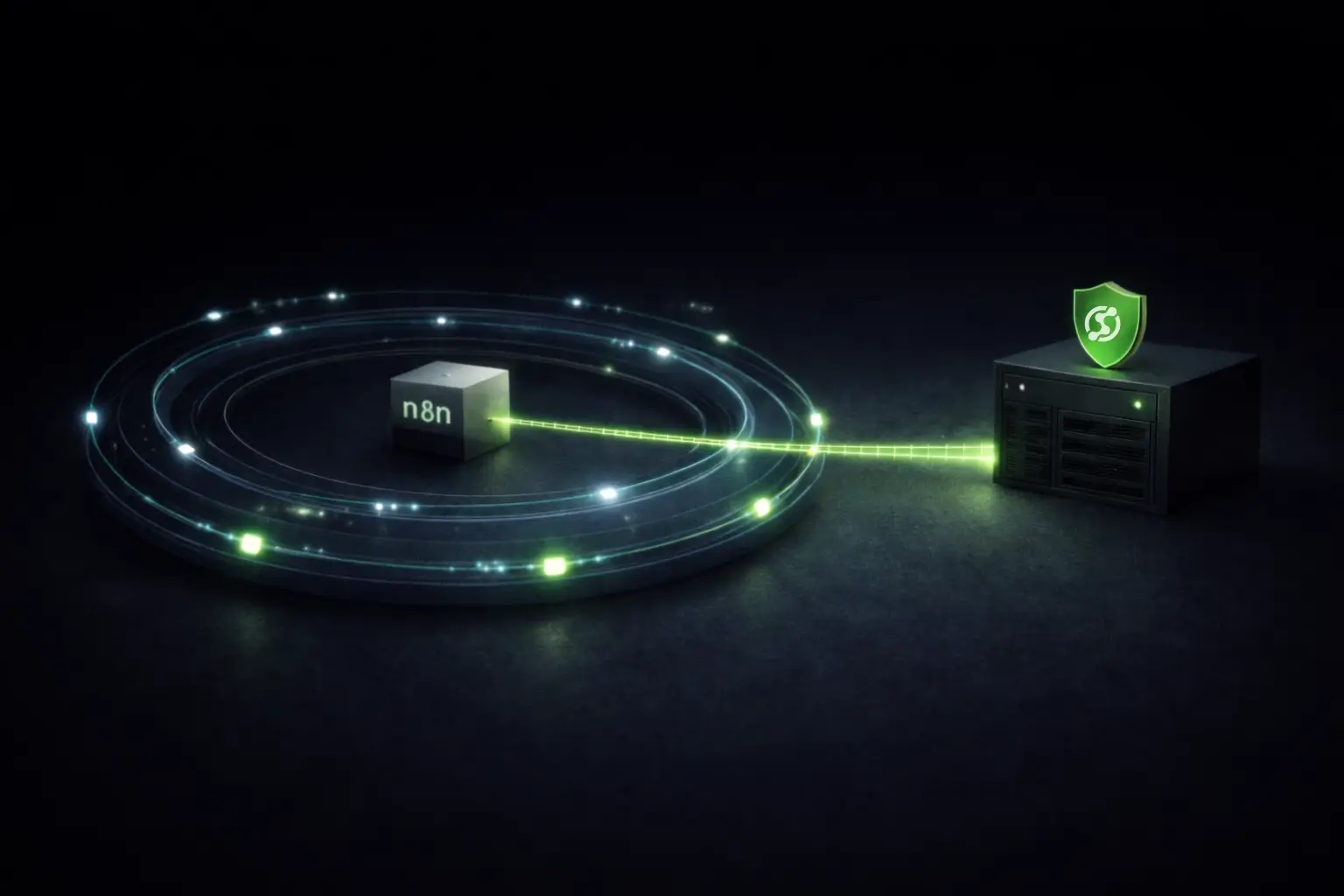
QuotaGuard works with Heroku, Render, Vercel, Railway, AWS Lambda, n8n, Make, Zapier, and pretty much any platform where your code can make HTTP requests. No special infrastructure required. You add a proxy environment variable. Your HTTP library reads it. Static IPs flowing.
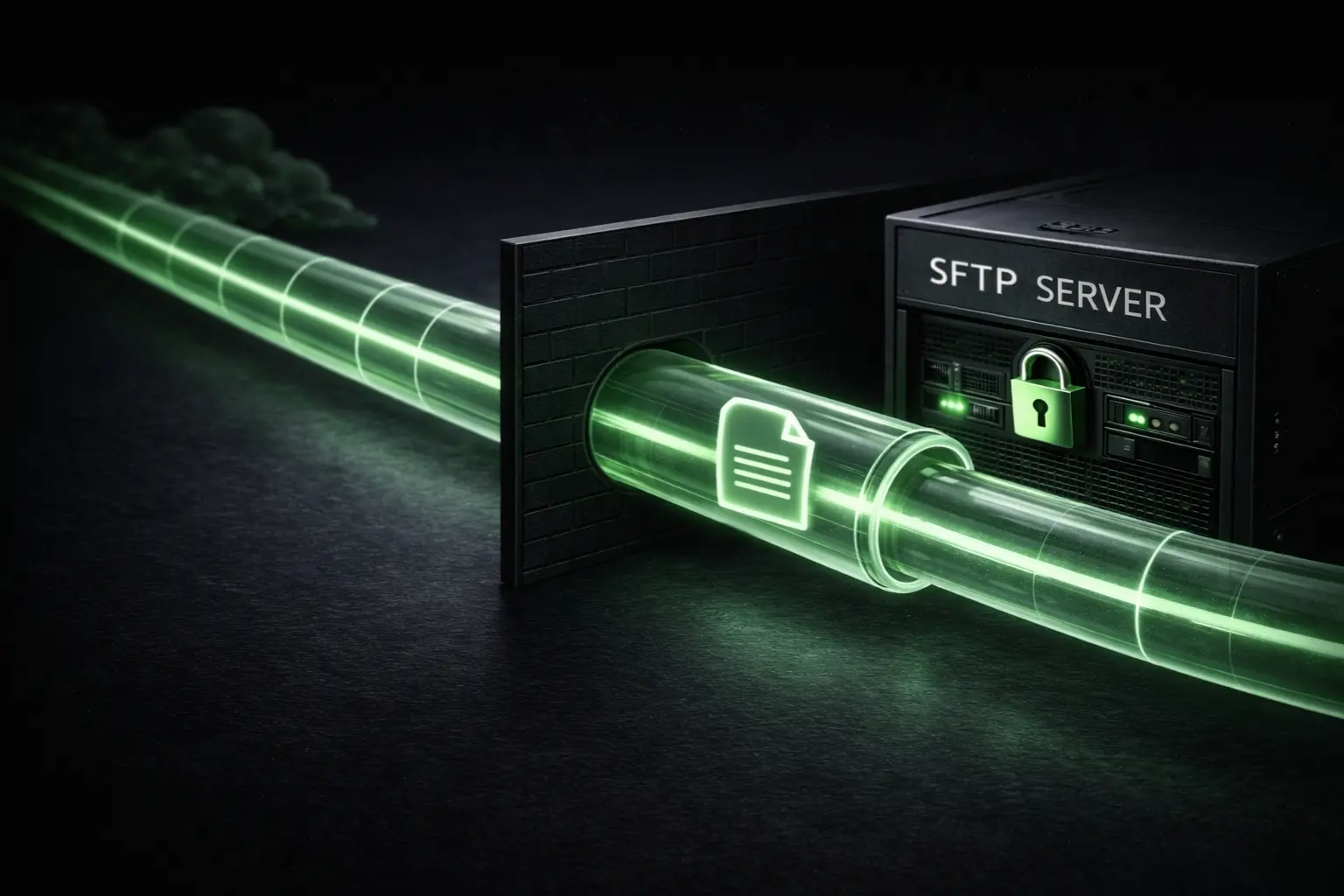
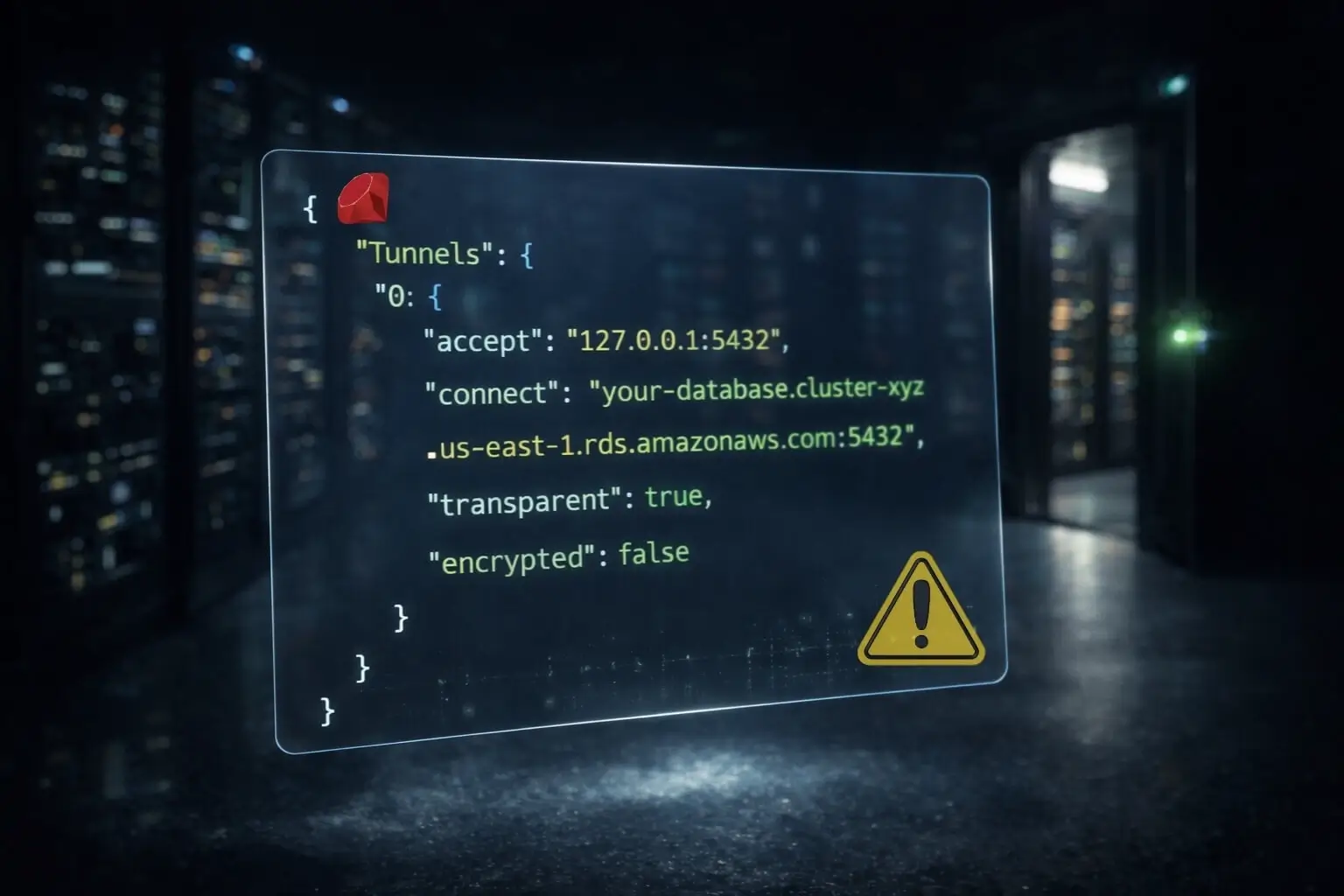
Shield for Extra Credit
If your auditor cares about encryption evidence, or if your customers require HIPAA or PCI compliance, QuotaGuard Shield adds SSL passthrough with end-to-end encryption. No TLS termination. No man-in-the-middle. Just encrypted tunneling through documented infrastructure.
Shield is $29/month to start. Worth considering if encryption in transit is part of your audit scope.
For geographic data residency (EU data stays in EU, US data stays in US), there's a $899/month add-on. That's relevant if you have enterprise customers with data sovereignty requirements.
The Audit Script
When your auditor asks, here's the gist of what you tell them:
"All outbound network traffic from our application routes through QuotaGuard's static proxy infrastructure. We have two documented IP addresses, load-balanced with automatic failover. External API calls and database connections are logged. Our IPs are whitelisted with upstream providers."
That covers CC6.1 network security controls for egress.
Getting Started
Sign up for QuotaGuard Static and get your two static IPs configured in under 20 minutes. Test them at https://ip.quotaguard.com. You'll see the same IP every time. That's the IP you document in your SOC 2 audit.
QuotaGuard Static starts at $19/month.
QuotaGuard Static IP Blog
Practical notes on routing cloud and AI traffic through Static IPs.





















.webp)




.webp)


.webp)





.webp)


.webp)

.webp)




.%20Three%20Options%20Compared%20(1).webp)
.webp)




.webp)






.webp)










.webp)




