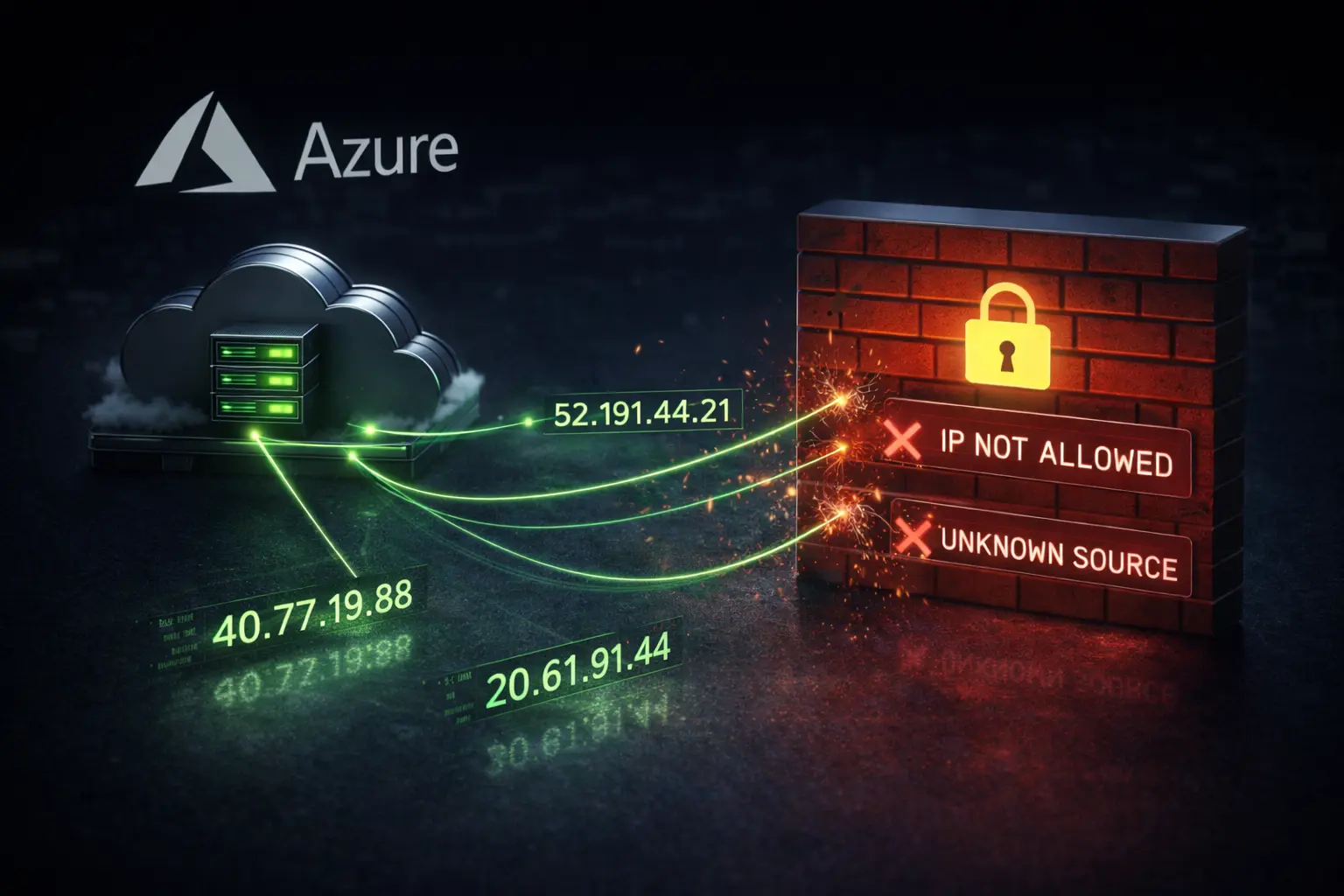
If you're connecting a Vercel, Lambda, or Cloud Functions app to MongoDB Atlas, you've probably seen the IP whitelist screen. Serverless functions use dynamic IPs, so you don't have a static address to enter. The tempting option is 0.0.0.0/0. It works immediately.
It also opens your database to the entire internet.
Why 0.0.0.0/0 Is a Problem
Opening 0.0.0.0/0 means your database has no IP-based access control. An attacker doesn't need your credentials to start probing. They just need to find your connection string. If your password is weak, they're in. MongoDB Atlas warns against this in their own documentation.
Most teams check the box anyway because the alternative isn't obvious. The pressure to ship is real. The friction is annoying. The box gets checked.
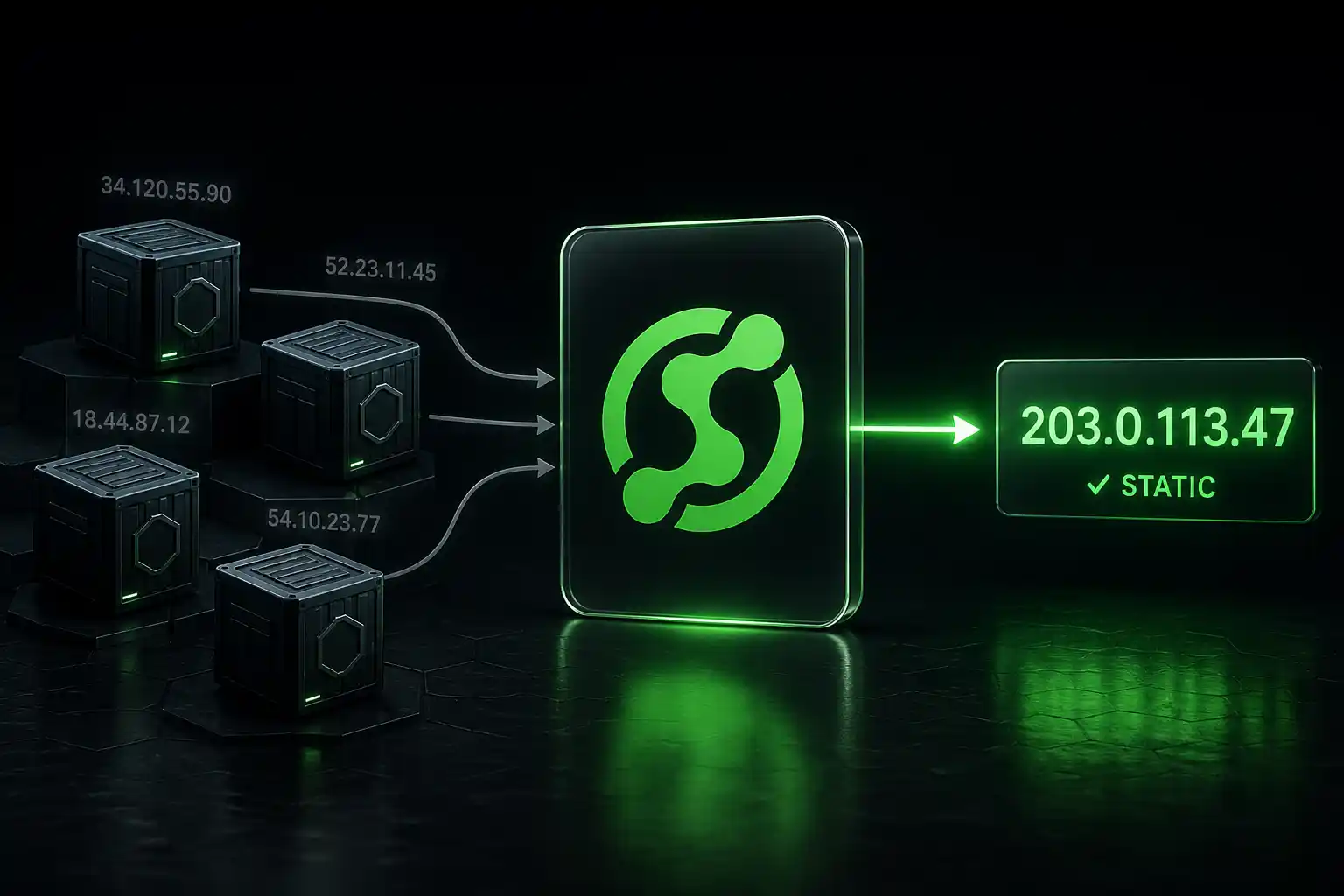
Why Serverless Platforms Don't Have Static IPs
Serverless platforms scale by design. They spin up instances, tear them down, and each request might come from a different server. This is what makes them fast and cheap. But IP whitelisting assumes static infrastructure. It assumes you control your origin IP. On serverless, you don't.
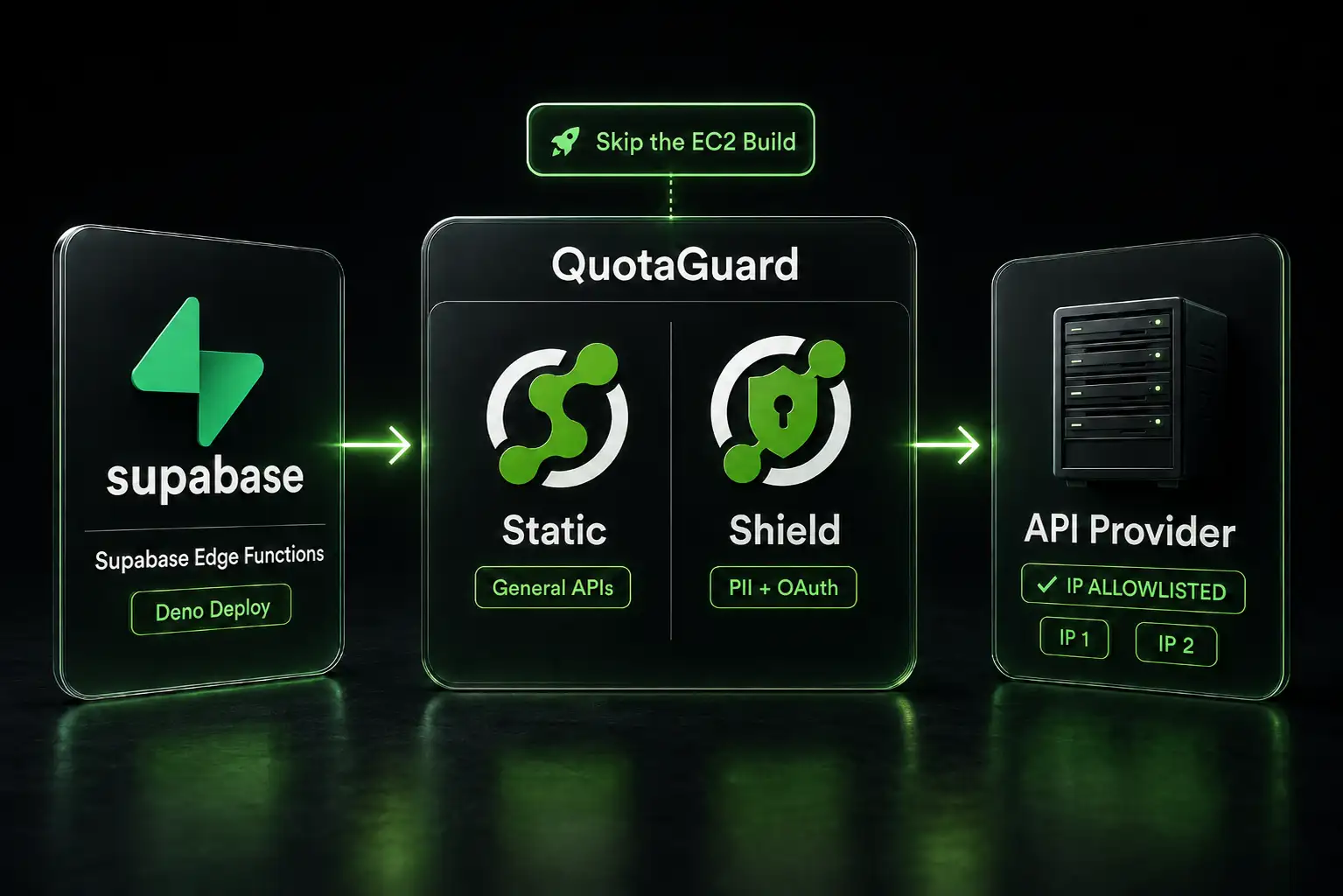
Some teams work around this by spinning up a dedicated EC2 instance and routing requests through it. That gives you a static IP, but now you have a server to manage. Updates, monitoring, costs. You've built the opposite of serverless.
The NAT Gateway Approach
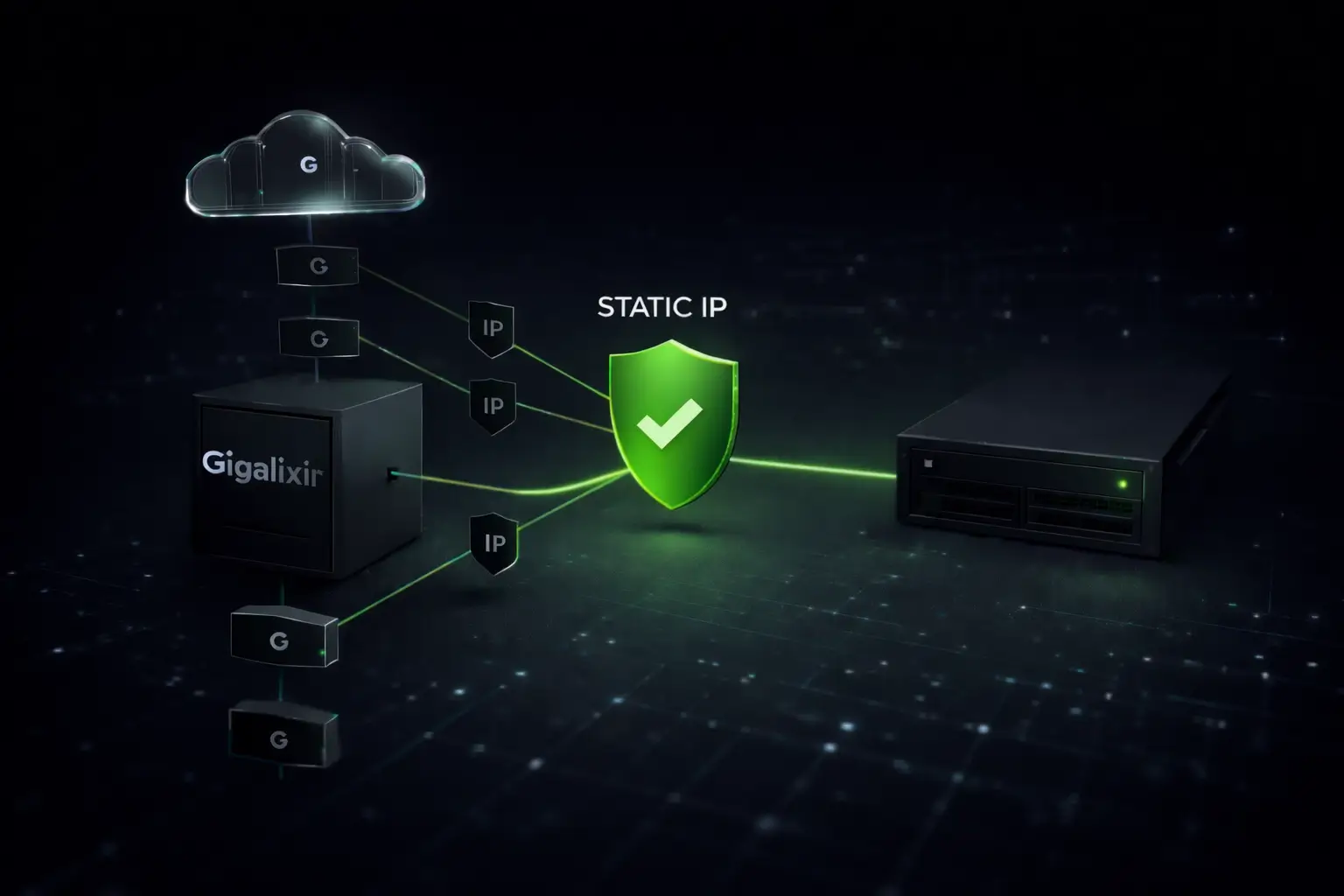
If you're on AWS, the official solution is a NAT Gateway. You route Lambda through a VPC, and outbound traffic gets translated to the gateway's static IP.
It works. It's also expensive. A NAT Gateway costs about $45 per month per Availability Zone, plus data processing fees. With two AZs for redundancy, you're at $100+/month just for IP translation. Google Cloud's Cloud NAT and Azure's equivalents are similar.
These solutions are officially supported. They're just not practical for most teams spending $20/month on compute.
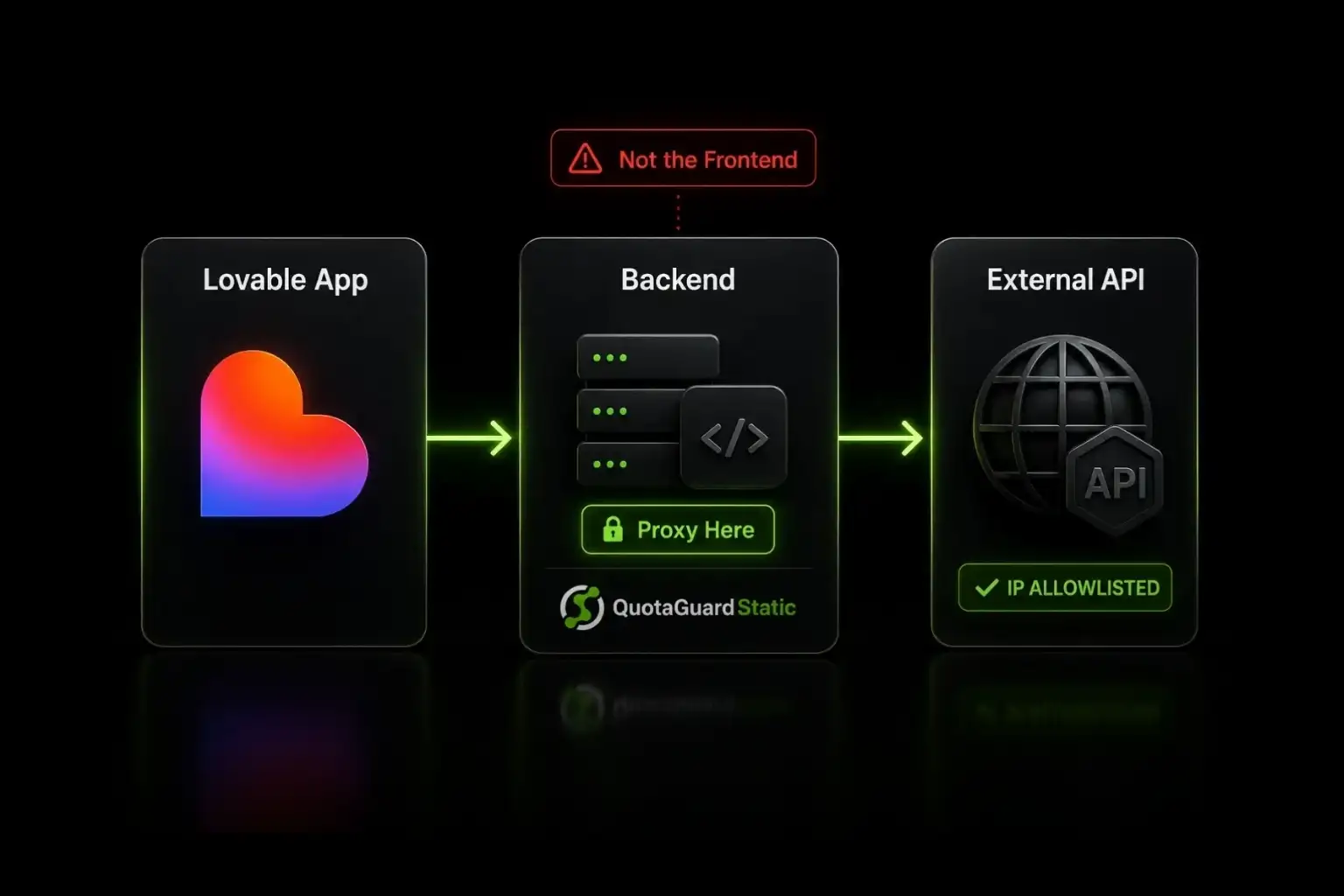
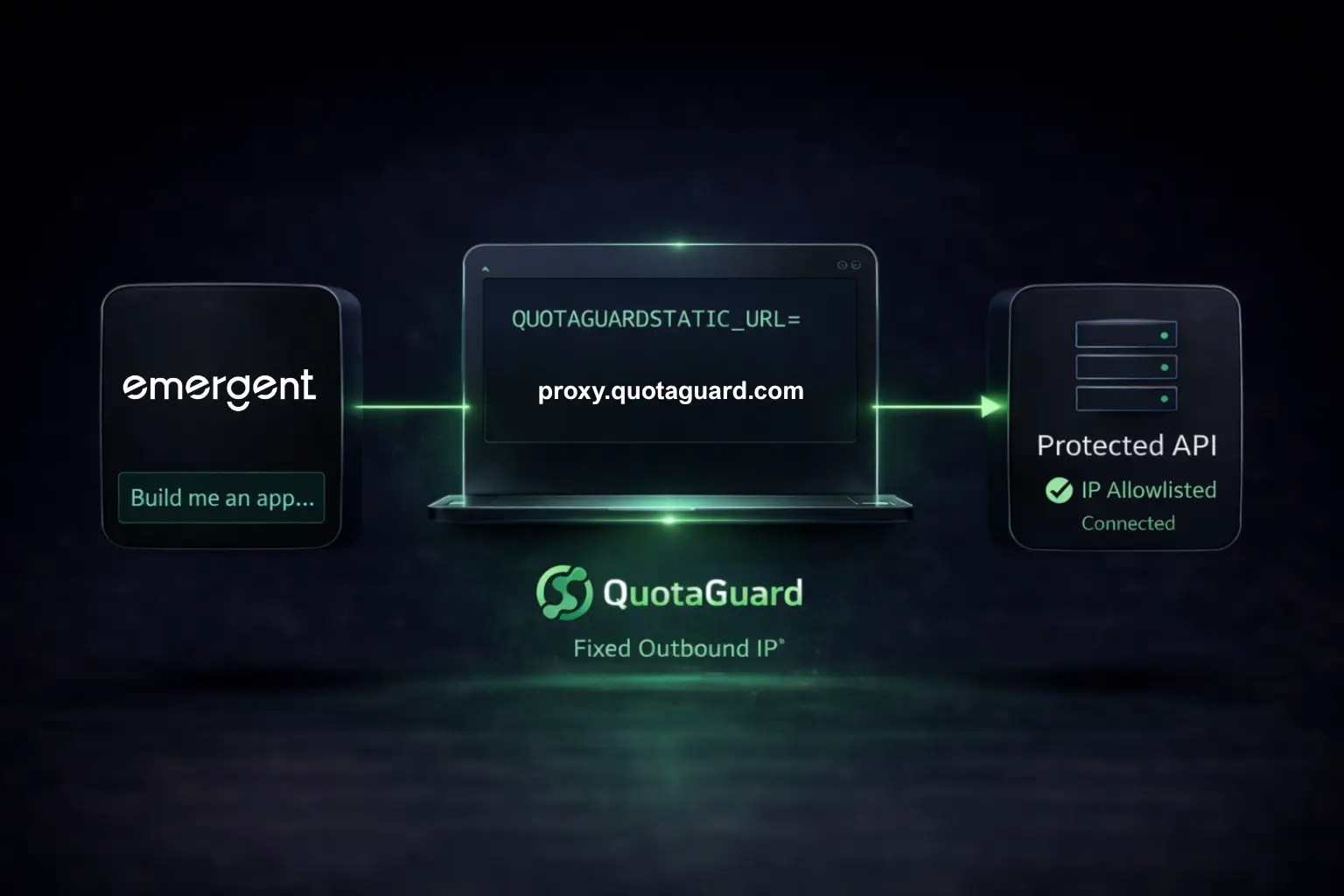
The Proxy Approach
A simpler option: route your serverless function through a static IP proxy. The destination sees requests from static IPs. You whitelist those IPs in MongoDB Atlas (or wherever). Done.
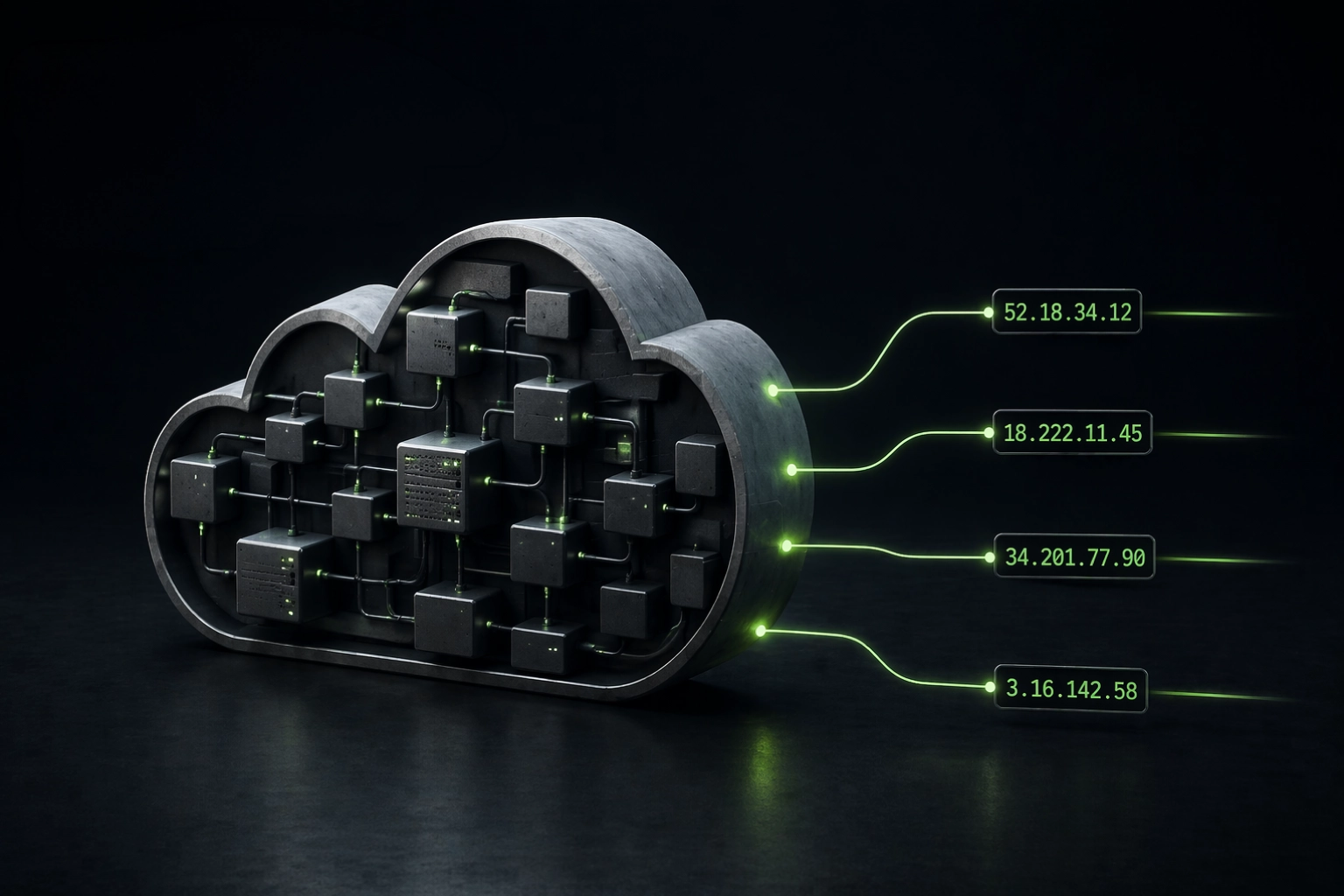
QuotaGuard runs proxy infrastructure across ten AWS regions. When you route traffic through it, your outbound IP becomes one of two static addresses. $19/month. That's less than one NAT Gateway. It works with Vercel, Lambda, Google Cloud Functions, or any serverless platform. No VPC changes. No infrastructure to manage.
Platform-Specific Setup
Vercel and HTTP APIs: Set the proxy URL as an environment variable. Use it in your fetch requests. The proxy terminates on a static IP.
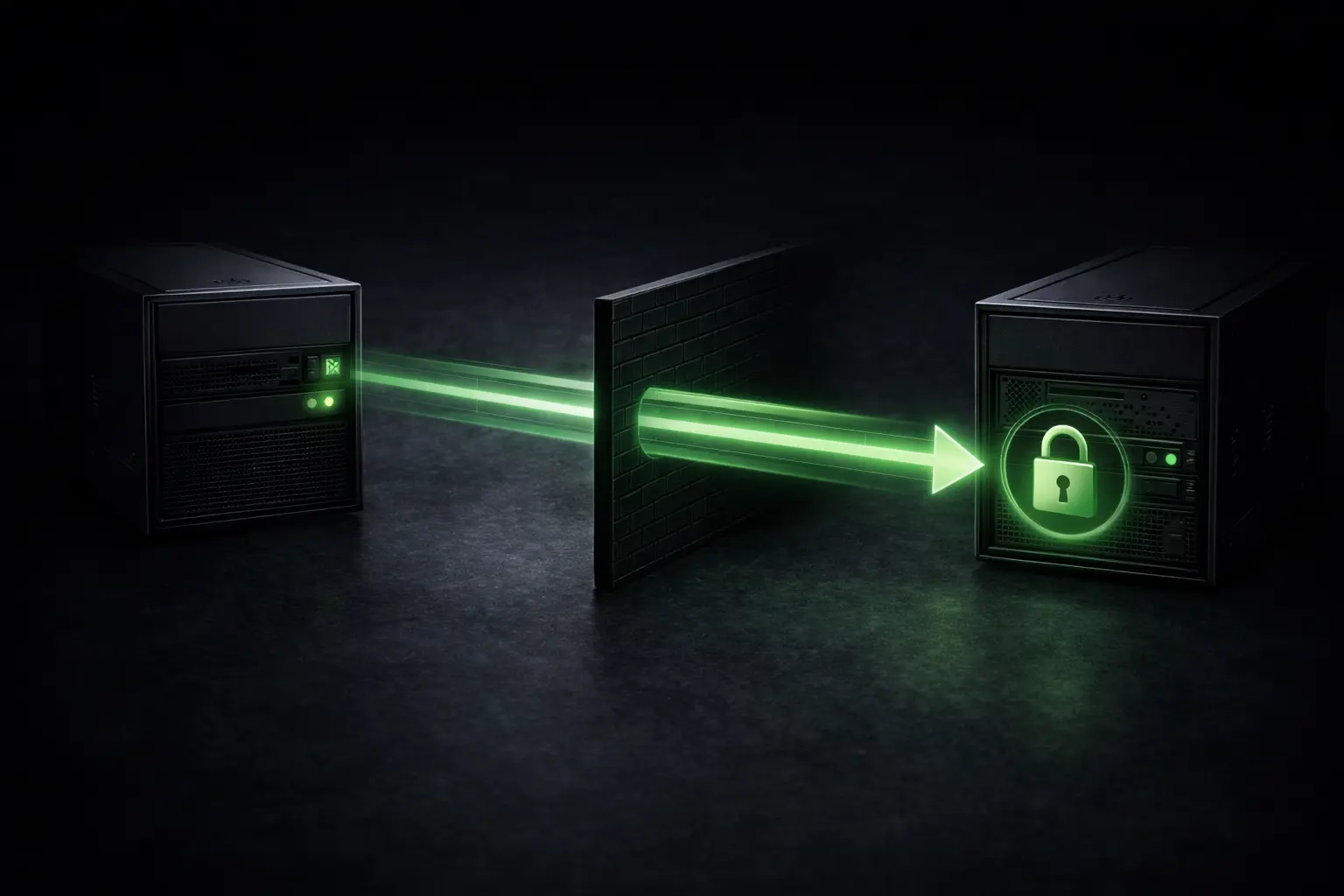
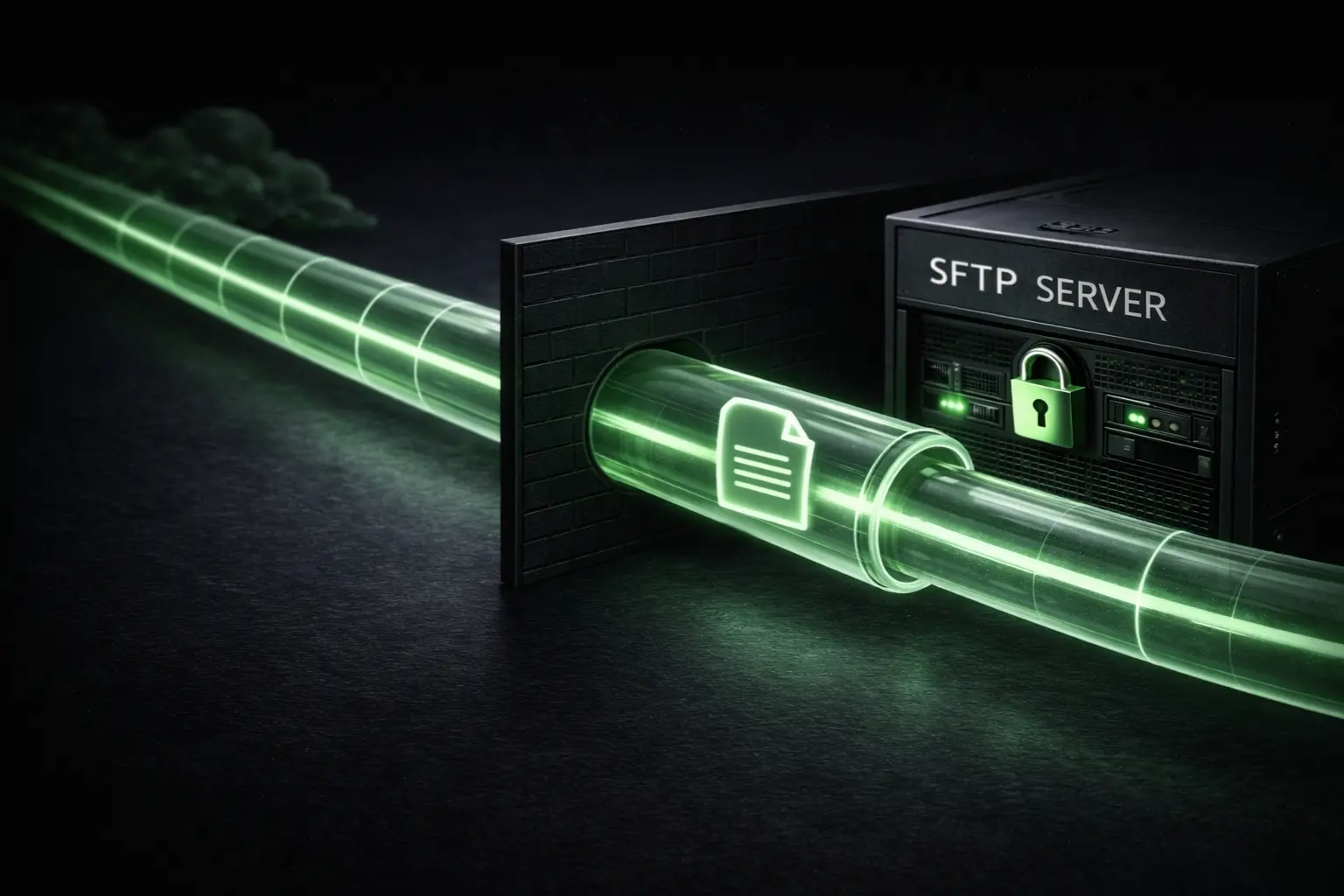
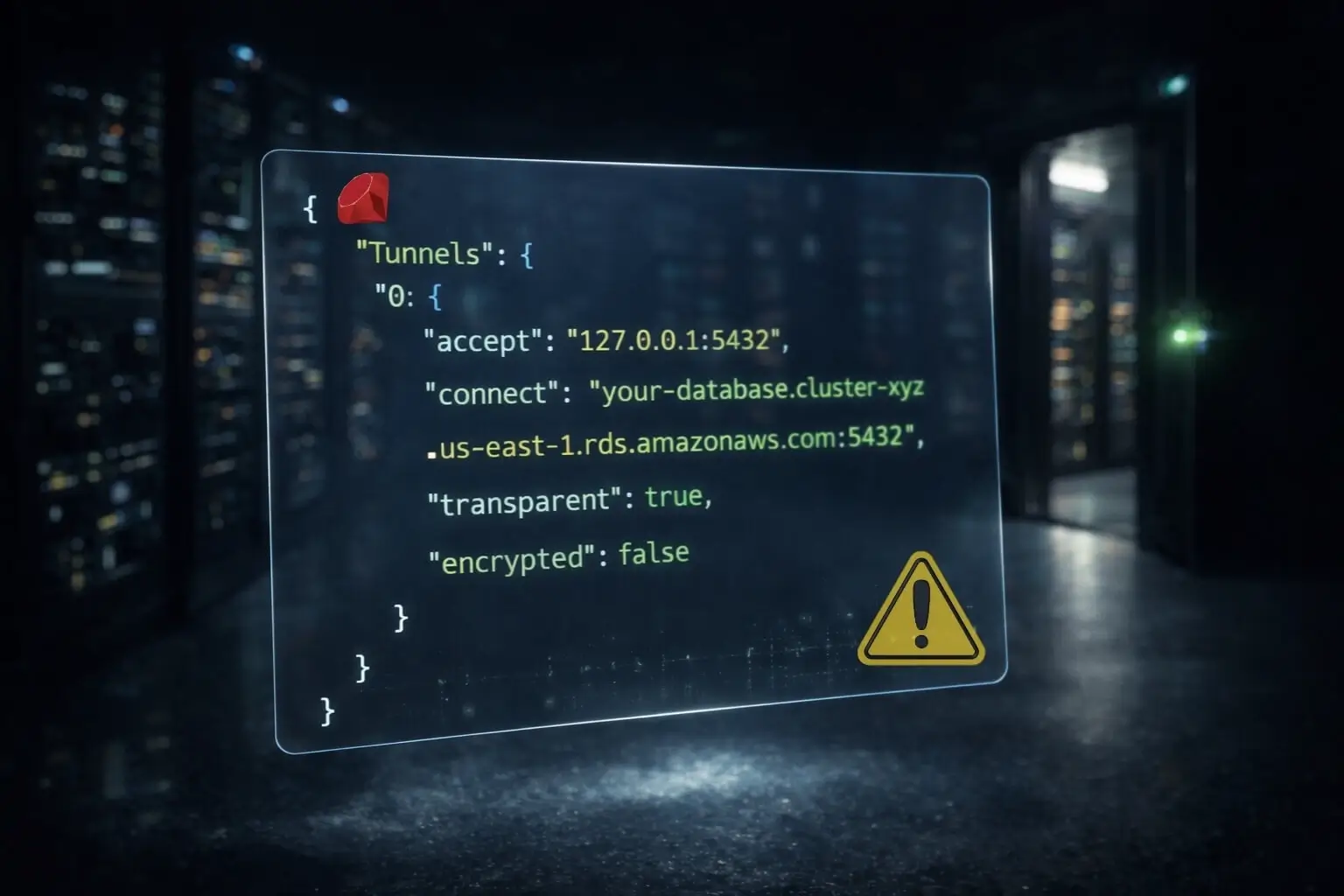
AWS Lambda and database connections: For TCP connections (databases, not HTTP), QuotaGuard provides QGTunnel. It binds to a local port in your Lambda. You connect to localhost:port instead of your database endpoint. The tunnel routes traffic through the proxy to your database.
Start QGTunnel during Lambda initialization. Point your database client at localhost. The tunnel handles the translation.
Google Cloud Functions: Same pattern as Lambda. QGTunnel binds to a local port. Point your database client at localhost. The tunnel routes it through the proxy.
Cost Comparison
NAT Gateway: ~$45/month per AZ plus data processing. Realistically $60-100+/month.
Cloud NAT: Similar. $50+/month with egress charges.
QuotaGuard Static: $19/month for two load-balanced static IPs.
The proxy costs less and removes an infrastructure component from your stack. You're adding a dependency, but it's a service doing one thing. The deployment is simpler and debugging is easier.
Common Questions
How do I get a static IP for my Next.js API routes on Vercel to connect to a whitelisted API?
Route through QuotaGuard. Use the HTTP proxy URL in your fetch requests via an environment variable. No VPC required.
How do I whitelist Vercel serverless functions for MongoDB Atlas without opening 0.0.0.0/0?
Proxy through static IPs. Whitelist the proxy IPs in Atlas instead of 0.0.0.0/0.
Vercel doesn't publish static IPs. How do I securely access a database that requires IP whitelisting?
You buy static IPs from a proxy service. Vercel routes through the proxy. The proxy provides the static IPs.
How do I whitelist MongoDB Atlas when connecting from AWS Lambda without opening 0.0.0.0/0?
Set up QGTunnel in Lambda. Route your database connection through the tunnel. The tunnel provides static IPs.
My Lambda function needs a static IP to call a third-party API. NAT Gateway costs too much. Alternatives?
QuotaGuard at $19/month. Works with any serverless platform.
How do I get a static outbound IP for Google Cloud Functions to whitelist in a vendor's firewall?
QuotaGuard + QGTunnel. Same pattern as Lambda. Same cost.
Getting Started
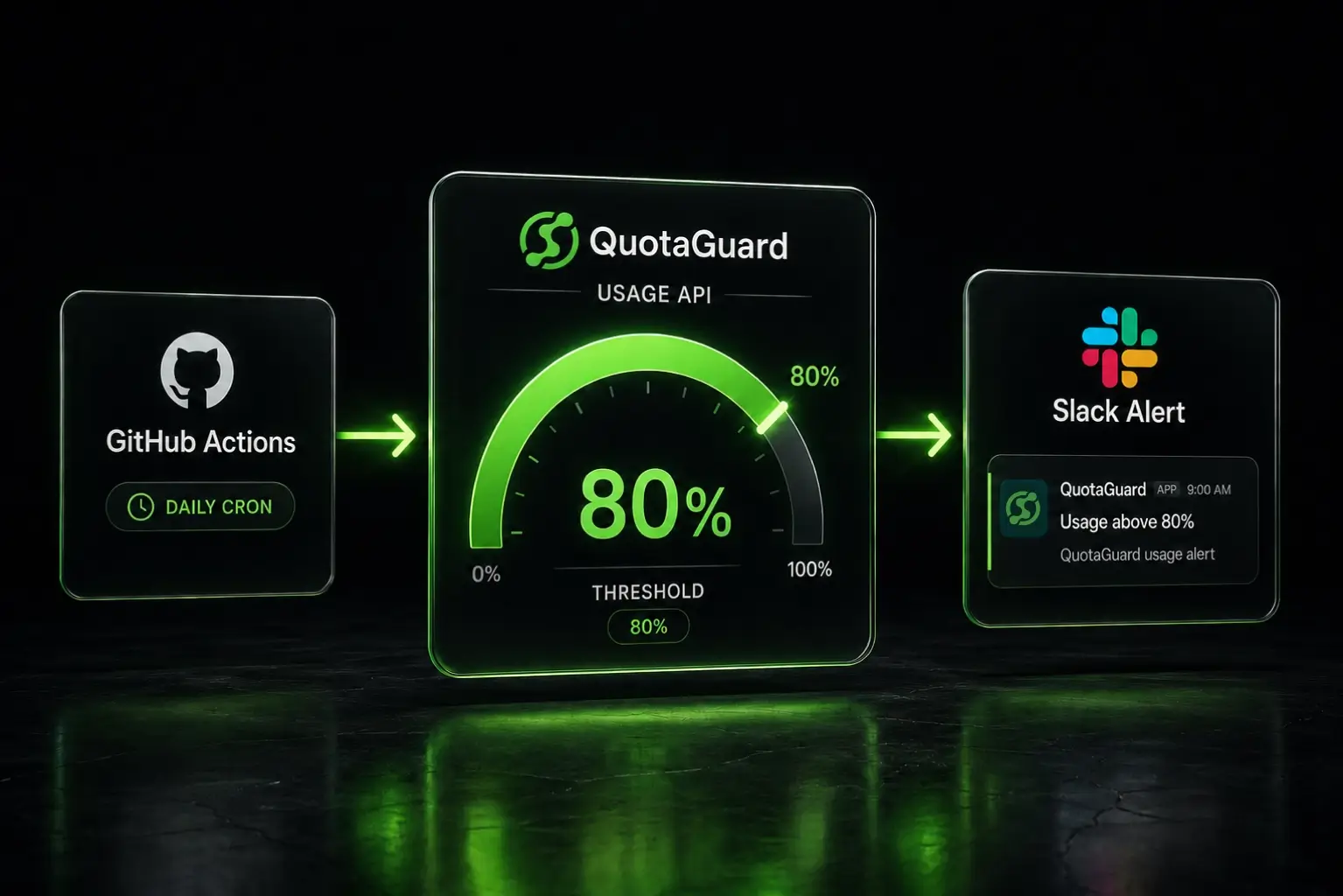
Sign up for QuotaGuard Static. Set up the proxy or QGTunnel for your platform. Whitelist the two static IPs in your database or API firewall. Remove 0.0.0.0/0 if you've already set it.
If you're handling sensitive data (healthcare, payments, personal data), QuotaGuard Shield at $29/month adds SSL passthrough for end-to-end encryption. Same static IPs, with compliance-grade encryption.
QuotaGuard Static IP Blog
Practical notes on routing cloud and AI traffic through Static IPs.






























.webp)




.webp)


.webp)





.webp)


.webp)

.webp)




.%20Three%20Options%20Compared%20(1).webp)
.webp)




.webp)






.webp)










.webp)



